CISA Warns of Active Exploitation of High-Severity Apache ActiveMQ Vulnerability CVE-2026-34197

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has officially added a high-severity vulnerability affecting Apache ActiveMQ to its Known Exploited Vulnerabilities (KEV) catalog, following confirmed reports of active exploitation in the wild. The security flaw, identified as CVE-2026-34197, represents a critical risk to enterprise environments, as it allows authenticated attackers to execute arbitrary code on targeted systems. Apache ActiveMQ, a widely utilized open-source message broker, serves as a central hub for asynchronous communication between applications, making it a high-value target for threat actors seeking to pivot through corporate networks.
The inclusion of this vulnerability in the KEV catalog triggers a mandatory response for Federal Civilian Executive Branch (FCEB) agencies. Under the guidelines established by Binding Operational Directive (BOD) 22-01, these agencies are required to remediate the flaw within a strict two-week window, setting a deadline of April 30. While the mandate specifically applies to federal entities, CISA and cybersecurity experts are strongly urging private-sector organizations to follow suit, citing the historical tendency for ransomware groups and state-sponsored actors to prioritize ActiveMQ vulnerabilities.
A Decadelong Silent Threat Uncovered by AI
One of the most concerning aspects of CVE-2026-34197 is its longevity. Security researchers have determined that the underlying code flaw remained undetected in the Apache ActiveMQ codebase for approximately 13 years. The discovery was made by Naveen Sunkavally, a researcher at Horizon3.ai, who utilized the Claude AI assistant to assist in the identification and analysis of the vulnerability.
The successful use of artificial intelligence to uncover a 13-year-old "zero-day" highlights a shifting paradigm in vulnerability research. By leveraging Large Language Models (LLMs) to parse complex code structures, researchers are now able to identify subtle logic flaws that traditional automated scanning tools and human audits may have overlooked for over a decade. In this instance, the AI assisted in pinpointing a failure in input validation that could be leveraged for injection attacks.
The vulnerability stems from improper input validation within the broker’s configuration handling. Specifically, an authenticated user with sufficient privileges can manipulate the system into executing arbitrary code via injection. While the requirement for authentication provides a slight barrier to entry compared to unauthenticated flaws, the prevalence of credential theft and weak internal access controls means that the "authenticated" status does not significantly lower the real-world risk for many organizations.
Technical Analysis and Exploitation Mechanics
CVE-2026-34197 is characterized as a Remote Code Execution (RCE) vulnerability. In the context of a message broker like ActiveMQ, RCE is particularly devastating. Because ActiveMQ often sits at the intersection of multiple critical business applications—handling everything from financial transactions to internal telemetry—a compromise of the broker can lead to a total collapse of the application ecosystem it supports.
According to technical disclosures from Horizon3.ai, the exploitation involves the use of specific query parameters and transport protocols. Researchers found that threat actors could trigger the vulnerability by initiating suspicious broker connections using the brokerConfig=xbean:http:// query parameter. This method leverages the internal transport protocol known as "VM" (Virtual Machine transport), which allows clients to connect to each other inside the same Java Virtual Machine (JVM) without the overhead of network communication.
By injecting malicious configurations through these parameters, an attacker can force the ActiveMQ instance to fetch and execute remote code, effectively handing over control of the server. This type of "living-off-the-land" technique, where attackers use built-in features for malicious purposes, makes detection difficult for standard security software that may view these connections as legitimate administrative actions.
Global Exposure and the Threat Landscape
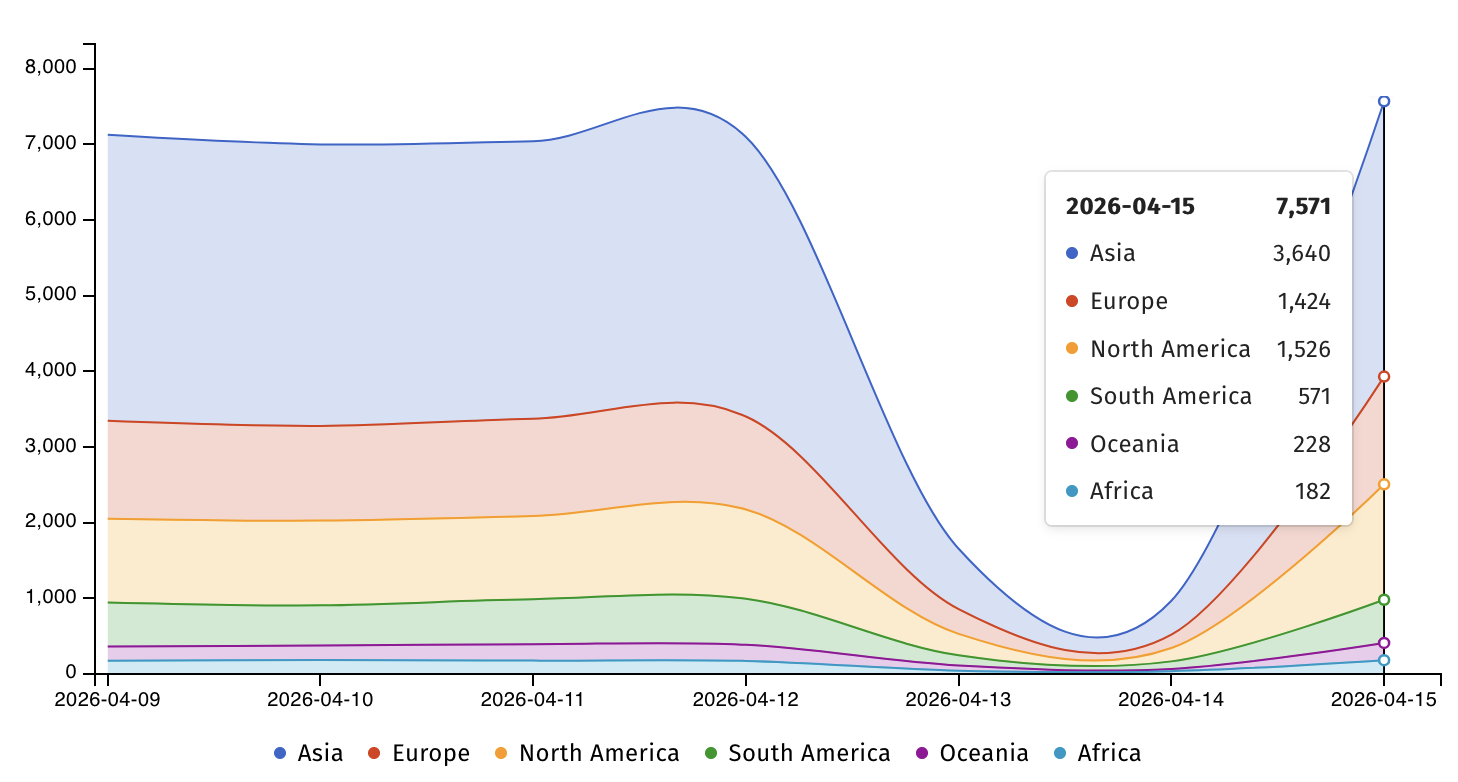
The scale of the potential attack surface is significant. Data provided by Shadowserver, a threat monitoring service, indicates that more than 7,500 Apache ActiveMQ servers are currently exposed to the public internet. While not all of these servers may be running the specific vulnerable versions, the high number of internet-facing instances provides a target-rich environment for opportunistic attackers.

Geographically, these exposed servers are distributed globally, with significant concentrations in the United States, China, Germany, and India. Organizations in the financial services, healthcare, and logistics sectors are particularly frequent users of ActiveMQ due to its ability to handle high-volume, reliable message queuing.
The cybersecurity community’s concern is heightened by the fact that ActiveMQ has been a recurring target for sophisticated cybercrime syndicates. In late 2023, another ActiveMQ vulnerability (CVE-2023-46604) was exploited by the TellYouThePass ransomware gang. In those attacks, the group utilized a remote code execution flaw to deploy file-encrypting malware across enterprise networks. The rapid weaponization of CVE-2023-46604 serves as a grim precedent for how quickly CVE-2026-34197 could be integrated into automated attack frameworks and ransomware-as-a-service (RaaS) kits.
Chronology of Response and Patching
The timeline for CVE-2026-34197 reflects a swift response from the Apache Software Foundation once the flaw was brought to their attention.
- Discovery: Researcher Naveen Sunkavally identifies the flaw using Claude AI and reports it to the Apache security team.
- March 30: Apache maintainers release security patches for ActiveMQ Classic. The fixes were implemented in versions 6.2.3 and 5.19.4.
- Early April: Security researchers begin publishing technical deep-dives, and threat intelligence platforms start seeing signs of scanning and exploitation attempts.
- April 16: CISA officially adds the vulnerability to the KEV catalog, citing evidence of active exploitation.
- April 30: The deadline for federal agencies to complete patching under BOD 22-01.
Apache has released security advisories detailing the necessary updates. For organizations running ActiveMQ Classic, upgrading to the latest versions (6.2.3 or 5.19.4) is the primary and most effective mitigation strategy.
Detection and Mitigation Recommendations
For organizations that cannot immediately apply patches, security experts recommend a multi-layered defense strategy. The first step is visibility. Horizon3 researchers suggest that administrators carefully analyze ActiveMQ broker logs for any entries containing the brokerConfig=xbean string, particularly when associated with the VM transport protocol.
Additional recommended actions include:
- Network Segmentation: Ensure that ActiveMQ servers are not directly accessible from the public internet unless absolutely necessary. Use VPNs or Zero Trust Network Access (ZTNA) solutions to gate access.
- Least Privilege: Review the permissions of authenticated users within the ActiveMQ environment. Restrict the ability to modify broker configurations to a minimal number of highly trusted administrative accounts.
- Egress Filtering: Implement strict outbound firewall rules on ActiveMQ servers to prevent them from communicating with external, unknown IP addresses. This can block the "callback" stage of an RCE attack where the server attempts to download a malicious payload.
- Endpoint Detection and Response (EDR): Deploy EDR tooling on the underlying hosts running ActiveMQ to monitor for suspicious child processes, such as the launching of cmd.exe or /bin/sh from a Java process.
Broader Implications for Enterprise Security
The exploitation of CVE-2026-34197 underscores the persistent risk posed by legacy code in modern infrastructure. The fact that a critical bug survived 13 years of technological evolution serves as a reminder that "old" software is not necessarily "secure" software. As organizations continue to build complex, interconnected systems, the message broker remains a critical point of failure.
Furthermore, the role of AI in this event cannot be overstated. While AI is frequently discussed as a tool for attackers to generate phishing emails or malware, this discovery demonstrates its potent capabilities in the hands of "white hat" researchers. However, this is a double-edged sword; as LLMs become more proficient at finding vulnerabilities, the window between the discovery of a flaw and its exploitation by malicious actors is likely to shrink even further.
CISA’s warning is a call to action for the global IT community. "This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise," the agency stated. By prioritizing the remediation of CVE-2026-34197, organizations can close a significant door to their internal environments and protect the integrity of their data pipelines.
As the April 30 deadline approaches for federal agencies, the private sector is expected to face a surge in automated scanning as threat actors attempt to capitalize on unpatched systems before the general population of administrators completes the update cycle. Security teams are advised to treat this as a high-priority event, mirroring the urgency shown by federal regulators.








