Cybercriminal Group TA558 Intensifies Attacks on Travel and Hospitality Sectors with Sophisticated Malware Campaigns

The global travel and hospitality industries, already grappling with the logistical nightmares of post-pandemic recovery, canceled flights, and staffing shortages, are facing a renewed and more sophisticated threat from the digital shadows. Security researchers have identified a significant escalation in activity from TA558, a long-standing threat actor that has pivoted its tactics to exploit the massive surge in travel bookings. According to a detailed technical analysis by the cybersecurity firm Proofpoint, this group has transitioned from traditional document-based exploits to more complex delivery mechanisms, including the use of container files like ISO and RAR, to deliver a diverse "potpourri" of malware designed to steal sensitive financial data and gain total control over infected systems.
This resurgence marks a pivotal shift for TA558, a group that has historically focused its efforts on Latin American organizations but has increasingly expanded its reach into North America and Western Europe. After a period of relative dormancy during the height of the COVID-19 pandemic—a lull likely caused by the global cessation of travel—the group has returned with a vengeance, launching 27 distinct campaigns in 2022 alone. This frequency is a staggering increase compared to the five total campaigns recorded between 2018 and 2021. The group’s primary objective remains financial gain, achieved through the exfiltration of customer data, credit card information, and corporate credentials.
The Evolution of TA558: From Macros to Container Files
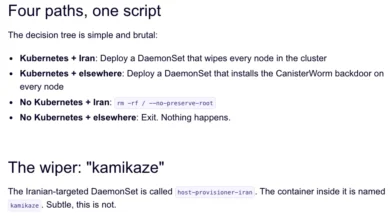
The hallmark of TA558’s recent activity is a calculated adaptation to the evolving security landscape. For years, the group relied heavily on malicious Microsoft Word documents that exploited the CVE-2017-11882 vulnerability—a remote code execution flaw in the Microsoft Equation Editor. They also utilized macro-laden Office documents and remote template injections to drop malware. However, the cybersecurity industry observed a significant tactical pivot in late 2021 and early 2022. This shift coincided with Microsoft’s announcement that it would begin disabling Visual Basic for Applications (VBA) and XL4 macros by default across its Office suite to mitigate phishing risks.
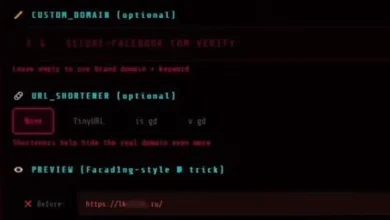
In response, TA558 moved away from document-based lures and began leveraging URLs that lead to compressed container files, such as ISO and RAR attachments. These file formats are particularly effective at bypassing traditional email filters that scan for executable files or malicious scripts. When a victim clicks a link in a fake reservation email, they are prompted to download a file. Once the user executes the file, it decompresses to reveal a series of nested scripts. In one documented instance, the execution of an ISO file triggered an embedded batch (BAT) file, which in turn called a PowerShell helper script. This script then downloaded the final payload: AsyncRAT, a powerful Remote Access Trojan.
A Chronology of Malicious Activity: 2018 to Present
The history of TA558 is characterized by a persistent focus on the travel sector, with its tactics evolving alongside defensive technologies.
2018: The Emergence
The group first came to the attention of security firms like Palo Alto Networks during "Operation Comando." During this period, the group primarily targeted Latin American hotel chains. Their methods were relatively straightforward, utilizing phishing emails with subject lines like "reserva" (reservation) written in Spanish or Portuguese. These emails contained Word documents exploiting the Equation Editor vulnerability to install Loda or Revenge RAT.
2019: Expansion of the Arsenal
TA558 began to diversify its delivery methods, incorporating malicious PowerPoint attachments and expanding its target demographic. For the first time, researchers observed English-language phishing lures, signaling the group’s intent to move beyond its traditional Latin American base.
2020: The Peak and the Pivot
Early 2020 saw a massive spike in activity. In January alone, the group launched 25 separate campaigns. However, as the COVID-19 pandemic brought the travel industry to a virtual standstill, TA558’s activity dropped precipitously. During this time, they continued to refine their use of RATs, with Cisco Talos reporting on the group’s use of Loda RAT to target both Windows and Android platforms.
2021-2022: The Resurgence
As travel restrictions lifted, TA558 ramped up its operations to unprecedented levels. The transition to URLs and container files became the standard operating procedure. Between 2018 and 2021, the group used URLs in only five campaigns; in 2022, that number jumped to 27. This period also saw the introduction of AsyncRAT into their toolkit, alongside their traditional favorites, Loda and Revenge RAT.
Technical Breakdown of the Malware Payload
The primary objective of TA558 is the installation of Remote Access Trojans (RATs). These programs allow attackers to maintain a persistent presence on a victim’s machine, providing a gateway for various malicious activities.
- AsyncRAT: An open-source remote administration tool that has been co-opted by cybercriminals. It allows for screen monitoring, keylogging, file management, and the execution of further commands. Its use of encrypted communication makes it difficult for network-based security tools to detect.
- Loda (LodaRAT): An AutoIt-based malware that is particularly adept at data theft. It can steal browser cookies, passwords, and even record audio through a computer’s microphone. Loda has been a staple of TA558 for years, frequently updated to include new obfuscation techniques.
- Revenge RAT: A well-known Trojan that provides comprehensive control over the infected host. It is often used for reconnaissance, allowing the attackers to determine the value of the infected machine before proceeding with further data exfiltration or ransomware deployment.
By deploying these RATs, TA558 can conduct extensive reconnaissance within a hotel or airline’s network. This allows them to identify systems that handle payment processing or store sensitive customer loyalty program data.
Industry Reactions and Expert Analysis
The resurgence of TA558 has prompted warnings from across the cybersecurity sector. Sherrod DeGrippo, Vice President of Threat Research and Detection at Proofpoint, emphasized the financial motivations driving the group. "TA558 is a persistent, active threat actor that has focused on the hospitality and travel industry for years," DeGrippo stated. "The group’s shift in tactics demonstrates a high level of adaptability. By moving to container files and URLs, they are successfully bypassing many of the common security measures that organizations have put in place to stop macro-based attacks."
Security analysts conclude with medium to high confidence that TA558 is motivated strictly by profit. Unlike state-sponsored groups that may seek political leverage or intellectual property, TA558 operates like a business. They use stolen data—ranging from credit card numbers to corporate credentials—to either steal money directly or sell the information on dark web forums. The impact is two-fold: the organizations suffer from data breaches, financial loss, and reputational damage, while individual travelers face identity theft and unauthorized charges on their accounts.
The travel industry is particularly vulnerable because of its reliance on high volumes of email communication with customers. Hotel front desk staff and reservation agents are trained to be helpful and responsive, making them prime targets for social engineering. A "reservation" email that appears to come from a stressed customer is often opened and acted upon quickly, bypassing the skepticism that might be applied to other types of unsolicited mail.
Broader Implications for the Travel Ecosystem
The activities of TA558 highlight a broader trend in the cybercrime world: the industrialization of phishing. As the group scales its operations, the potential for collateral damage increases. A compromise of a single large hotel chain or a regional airline can expose the personal data of hundreds of thousands of travelers.
Furthermore, the geographical shift of TA558 suggests that no region is safe. While Latin America remains a primary focus, the increase in English-language campaigns and targets in North America and Western Europe indicates that the group is following the money. The travel surge in these regions provides a target-rich environment for attackers who are looking for high-value victims.
From a technical standpoint, the move to ISO and RAR files underscores the "cat and mouse" game between attackers and defenders. As Microsoft and other software vendors close off old avenues of attack—like Office macros—adversaries will inevitably find new ones. The use of container files is a clever way to wrap malicious intent in a format that many users still perceive as "safe" or merely a technical necessity for large downloads.
Defensive Strategies and Recommendations
In light of TA558’s increased activity, security researchers recommend a multi-layered defense strategy for organizations in the travel and hospitality sectors.
- Email Filtering and Inspection: Organizations should update their email security gateways to specifically inspect and, if necessary, block ISO, RAR, and other container file types if they are not essential to business operations.
- User Awareness Training: Employees, particularly those in customer-facing and reservation roles, must be trained to recognize the signs of social engineering. They should be wary of any unsolicited email requesting they download and open files, even if the email pertains to a "reservation."
- Endpoint Protection: Deploying advanced endpoint detection and response (EDR) tools can help identify the execution of suspicious PowerShell scripts or batch files that often follow the opening of a container file.
- Network Segmentation: By segmenting networks, organizations can ensure that if a front-desk computer is compromised by a RAT, the attacker cannot easily move laterally to the servers containing sensitive customer payment data or employee records.
- Multi-Factor Authentication (MFA): Implementing MFA across all corporate accounts can prevent TA558 from using stolen credentials to gain deeper access to the corporate network.
As TA558 continues to refine its "reserva" lures and technical delivery methods, the travel industry must remain vigilant. The transition from the misery of travel delays to the misery of a cyber infection is only a single click away, making proactive defense and employee education more critical than ever in the post-pandemic era.