The Evolution of Underground Credit Card Marketplaces and the Rise of Professionalized Fraud Vetting Standards

The underground market for stolen credit card data has entered a new era of professionalization, shifting away from opportunistic, chaotic exchanges toward a structured, process-driven ecosystem designed to withstand both law enforcement scrutiny and internal criminal deception. Analysts from the cybersecurity firm Flare recently uncovered a comprehensive instructional document on a prominent underground forum titled "The Underground Guide to Legit CC Shops: Cutting Through the Bullshit," which serves as a definitive blueprint for how modern threat actors navigate an increasingly volatile illicit economy. This guide signifies a maturation of the "carding" world, where the primary concern for criminals is no longer just evading the police, but surviving a marketplace plagued by exit scams, low-quality data, and sophisticated "honeypots" managed by global authorities.
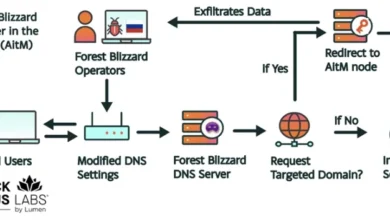
For decades, the sale of stolen credit card information—often referred to as "CCs" or "dumps"—was a relatively straightforward enterprise. Data was harvested through point-of-sale (POS) malware, phishing, or skimmers, and sold on centralized forums. However, a series of high-profile law enforcement operations, including the 2023 takedown of Genesis Market and the 2021 shuttering of Joker’s Stash, has fractured this environment. In response, the criminal element has been forced to adopt rigorous due diligence protocols that mirror the vetting processes of legitimate corporate procurement departments. The newly discovered guide provides an unprecedented look into this methodology, detailing how fraud actors now evaluate the reliability of their suppliers through a lens of operational security (OPSEC) and technical verification.
The Chronology of Instability: From Joker’s Stash to Modern Fragmentation
To understand why such a guide is necessary, one must look at the timeline of the underground credit card economy over the last five years. Between 2017 and 2021, the market was dominated by a few "behemoths" like Joker’s Stash, which at its peak generated hundreds of millions of dollars in revenue. When Joker’s Stash voluntarily "retired" in early 2021, it left a massive vacuum. This was followed by a series of aggressive international law enforcement actions, such as "Operation Cookie Monster" and the seizure of platforms like UniCC and Ferum Shop.
This period of 2021 to 2024 has been defined by extreme volatility. As major platforms fell, hundreds of smaller, unverified shops emerged to fill the void. Many of these were "exit scams," where operators would collect deposits from users and then vanish, or "ripper" sites that sold recycled, invalid, or outright fake data. The internal distrust within the criminal community reached a boiling point, necessitating a standardized way to identify "legitimate" criminal enterprises. The Flare-analyzed guide is a direct byproduct of this era of instability, offering a survival manual for actors who can no longer trust the traditional markers of a successful marketplace.

Redefining Legitimacy: Survival as a Business Metric
According to the Flare analysis, the underground guide reframes the concept of legitimacy within the carding community. In a legal business context, legitimacy is tied to registration and compliance; in the carding world, it is defined by "survivability." A shop is considered "legit" if it can maintain operational continuity despite constant pressure from the FBI, Europol, and rival hacking groups. The document emphasizes that branding, flashy user interfaces, and high-volume advertising are often red flags rather than signs of success. Instead, threat actors are encouraged to look for shops that prioritize technical resilience over marketing.
A critical component of this legitimacy is the quality of the "freshness" of the data. The guide highlights the importance of "fresh BINs" (Bank Identification Numbers). The BIN constitutes the first six to eight digits of a credit card and identifies the issuing bank and card type. High-tier shops are those that can consistently source data from recent "infostealer" infections or real-time phishing kits, ensuring that the cards have not yet been flagged by bank fraud detection algorithms. The guide suggests that a shop’s reputation is built on its "decline rate"—the percentage of cards that fail at the point of transaction. Shops that maintain low decline rates are prioritized, as they demonstrate a direct pipeline to active, compromised systems.
Technical Vetting Protocols: A Step-by-Step Approach
The guide introduces a rigorous technical checklist that fraud actors use to conduct due diligence on a marketplace before committing funds. These steps involve a level of technical scrutiny that suggests even mid-tier criminals are becoming more sophisticated in their analytical capabilities.
- Domain and Infrastructure Analysis: Actors are advised to check the age of a domain and its WHOIS privacy settings. A shop that has existed for several years is viewed with more trust than a "pop-up" shop. Furthermore, the presence of SSL certificates and DDoS protection is now a baseline requirement.
- Mirror Infrastructure: The guide notes that mature operations rarely rely on a single URL. Legitimate shops typically maintain multiple mirror domains and backup access points, often accessible only via the Tor network or I2P (Invisible Internet Project). This redundancy is seen as proof that the operators have invested in long-term infrastructure.
- Social Intelligence: Rather than trusting on-site testimonials, which are easily faked by site owners, the guide directs users to closed, invite-only forums. It encourages actors to track the "history" of a vendor’s username across multiple platforms, looking for patterns of behavior and consistent feedback from established community members.
- Coordinated Endorsement Detection: A sophisticated aspect of the vetting process involves identifying "shilling"—the use of sock-puppet accounts to post fake positive reviews. The guide teaches actors to look for multiple endorsements from accounts created on the same day or accounts that only post reviews for a single shop.
The Shift to Financial Anonymity and Advanced OPSEC
Operational security is perhaps the most emphasized section of the newly discovered guide. As blockchain analysis tools used by law enforcement have become more effective, the carding community has shifted its financial strategies. The guide strongly discourages the use of Bitcoin for direct transactions due to its transparent ledger. Instead, it advocates for the use of Monero (XMR), a privacy-focused cryptocurrency that obscures sender, receiver, and transaction amounts.
Beyond currency, the guide outlines a "layered" approach to operational security that mirrors the tactics of advanced persistent threat (APT) groups. Users are instructed to never access carding shops from their primary operating system. Instead, they are told to use dedicated Virtual Machines (VMs) or "Live" operating systems like Tails, which route all traffic through Tor and leave no digital footprint on the hardware. The use of high-quality proxies or SOCKS5 residents is also recommended to ensure the actor’s IP address matches the geographic location of the stolen credit card, thereby bypassing "velocity checks" and location-based fraud triggers used by merchants.
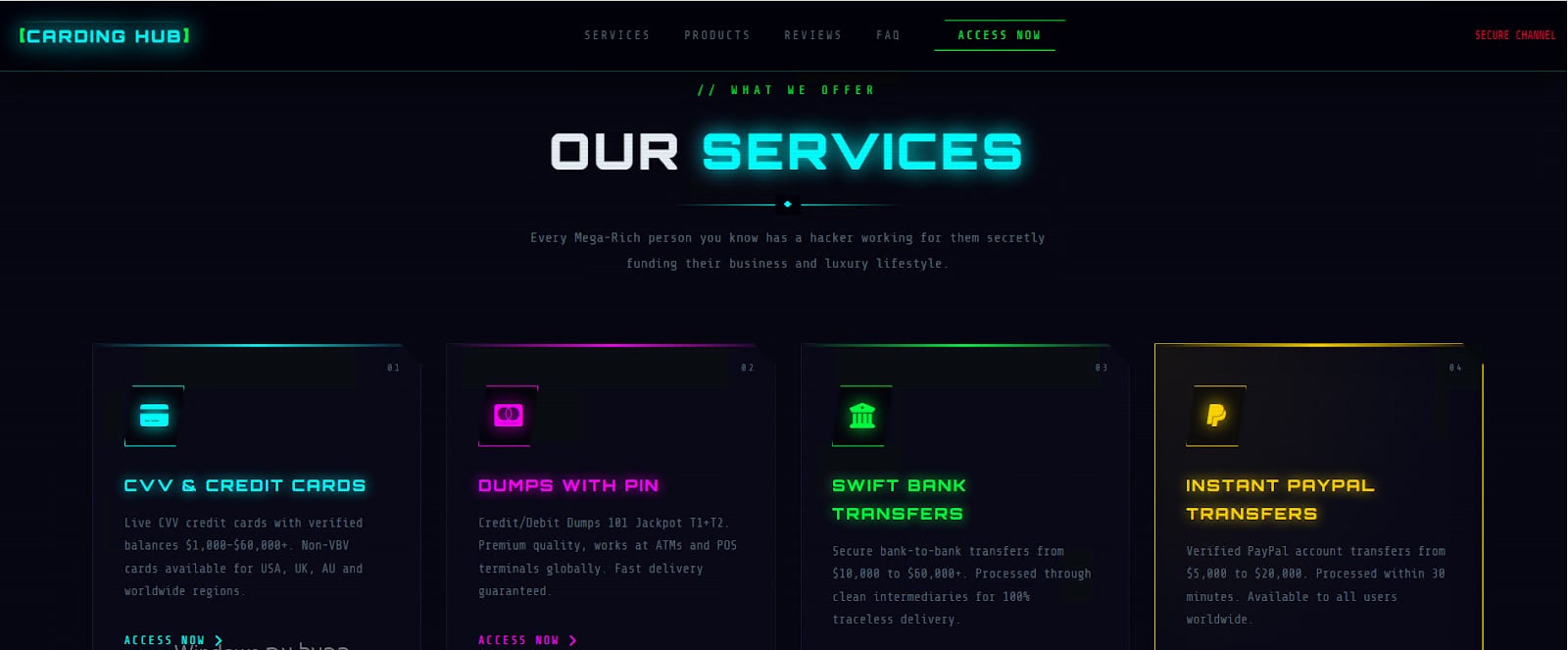
Market Segmentation: Automated Platforms vs. Boutique Vendors
The Flare analysis reveals a clear bifurcation in the underground economy: the rise of massive automated platforms versus exclusive boutique vendors. Automated platforms function much like legitimate e-commerce sites, featuring search filters for specific banks, card levels (Gold, Platinum, Business), and geographic locations. These are designed for "bulk" actors who operate at scale and accept a certain percentage of "dead" cards as a cost of doing business.
In contrast, the guide highlights the value of "boutique" groups. These are often smaller, private circles that do not advertise on public-facing dark web forums. Access is granted only through referrals. These vendors offer higher-quality data, often sourced from specific, high-value breaches, and provide a level of customer service—including "replacement guarantees" for dead cards—that automated platforms cannot match. This segmentation shows that the underground economy is diversifying to meet the needs of different "classes" of cybercriminals.
Broader Impact and Defensive Implications
The professionalization of the carding market has significant implications for the global financial sector. As threat actors become more disciplined in their vetting and OPSEC, the "window of opportunity" for banks to detect and cancel stolen cards is shrinking. The move toward Monero and encrypted communication makes it increasingly difficult for law enforcement to "follow the money," which has traditionally been the most effective way to dismantle these networks.
Industry experts suggest that this shift toward structured vetting will likely lead to a higher "success rate" for fraud campaigns. When criminals use higher-quality, vetted data and better OPSEC, the financial losses per incident are likely to increase. For cybersecurity teams, this means that traditional defense-in-depth strategies must be updated. Monitoring for "leaked credentials" is no longer enough; organizations must now gain visibility into the vetting forums themselves to understand which of their specific BINs are being targeted and which shops are currently holding their customers’ data.
The discovery of "The Underground Guide to Legit CC Shops" serves as a stark reminder that the cybercriminal landscape is a living, evolving organism. It responds to pressure with adaptation. By adopting corporate-style vetting, technical due diligence, and advanced financial privacy, the carding community is attempting to build a resilient, "trustless" economy that can operate in the shadows of the legitimate world indefinitely. For defenders, the challenge is no longer just stopping a hack, but understanding the complex supply chain that monetizes the fallout of that hack. Understanding these internal criminal standards is the first step in developing the proactive, intelligence-driven defenses necessary to disrupt them.