Operation PowerOFF identifies 75k DDoS users, takes down 53 domains

The Mechanics of DDoS-for-Hire and the Rise of Booter Services
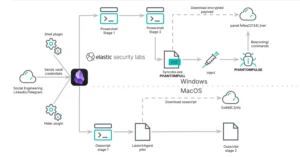
At the heart of Operation PowerOFF is the targeting of "booter" or "stresser" services. These are web-based platforms that simplify the process of launching DDoS attacks, allowing even those with minimal technical expertise to overwhelm a target’s network with a massive influx of internet traffic. By paying a small subscription fee—often as low as $10 to $20—users can rent the processing power of large-scale botnets. These botnets typically consist of thousands of compromised "Internet of Things" (IoT) devices, such as smart cameras, home routers, and digital video recorders, which have been infected with malware and hijacked by cybercriminals.
The allure of these services lies in their accessibility. While traditional hacking requires deep knowledge of exploit development or network vulnerabilities, booter services provide a user-friendly interface. A customer simply enters the IP address or domain of their target, selects the duration and intensity of the attack, and clicks a button to initiate the "boot." To maintain a veneer of legality, many of these platforms market themselves as "stress testing" tools designed for network administrators to test their own infrastructure’s resilience. However, law enforcement officials have long argued that these claims are fraudulent, as the platforms lack any mechanism to verify that the user has permission to test the targeted network. In reality, these services are used almost exclusively for malicious purposes, ranging from competitive advantages in online gaming to the systematic extortion of small businesses.
A Chronology of Operation PowerOFF: From Inception to Global Sprint
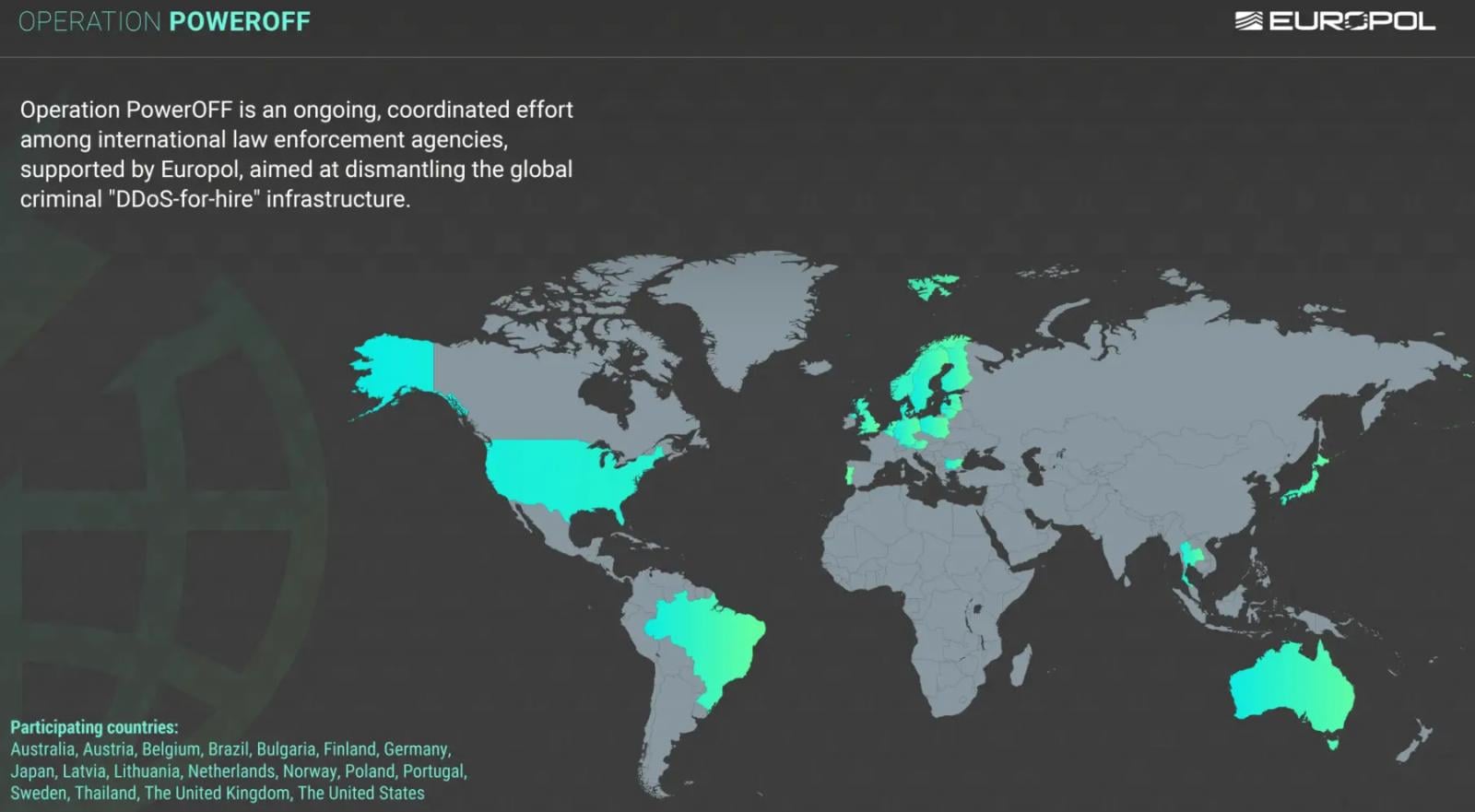
Operation PowerOFF is not a singular event but a sustained, multi-year campaign that has evolved alongside the shifting tactics of cybercriminals. The operation first gained major international attention in late 2022 when the U.S. Department of Justice, in coordination with the FBI and the National Crime Agency (NCA) of the United Kingdom, announced the seizure of 48 of the world’s most popular booter domains. That initial phase revealed the staggering scale of the industry, with some platforms facilitating hundreds of thousands of attacks.
Following the 2022 takedown, investigators shifted their focus from the infrastructure providers to the users themselves. Throughout 2023 and into early 2024, a series of "operational sprints" took place. These sprints were intensive periods of cross-border collaboration where digital forensics experts from national authorities worldwide gathered to share intelligence and execute targeted actions. The goal was twofold: to dismantle the technical backends that remained and to gather evidence on high-value targets—individuals who were either frequent customers of these services or who were reselling attack capacity to others.

The most recent phase, which involved countries as diverse as Australia, Thailand, Japan, Brazil, and the United States, represents the most comprehensive crackdown to date. By executing 25 search warrants and making four key arrests, authorities have sent a clear message that the anonymity previously associated with booter services is a thing of the past.
Data-Driven Enforcement: Identifying 75,000 Participants
One of the most striking revelations of the latest Operation PowerOFF update is the sheer volume of users identified. Law enforcement agencies managed to gain access to the backend databases of several seized platforms, uncovering a treasure trove of user data. This included email addresses, IP logs, payment records (often involving cryptocurrencies), and communication histories.
Of the 75,000 individuals identified, many have begun receiving formal warnings via email or physical letters. These notifications serve as a "knock-and-talk" in digital form, informing the recipients that their activities have been logged and that they are now on a law enforcement watchlist. For many younger users—often teenagers or young adults who view DDoS attacks as a harmless prank within the gaming community—these warnings are intended to be a deterrent before they escalate into more serious forms of cybercrime.
The data seized also revealed that the booter economy is remarkably resilient. When one domain is seized, users often migrate to mirrors or competing services within hours. To combat this, the latest phase of the operation focused on seizing 53 domains simultaneously, creating a vacuum in the market and making it significantly harder for users to find reliable platforms.
Shifting to a Prevention-First Strategy
Recognizing that arrests and seizures alone cannot entirely solve the problem of DDoS attacks, Europol and its partners are transitioning Operation PowerOFF into a proactive prevention phase. This strategy acknowledges the psychological profile of the typical booter user: often young, technically curious, and unaware of the severe legal consequences of their actions.

One of the more innovative aspects of this new phase is the use of search engine optimization (SEO) and advertising as a tool for disruption. Law enforcement agencies have begun placing targeted ads on search engines like Google and Bing. When a user searches for terms like "DDoS tool," "buy booter service," or "how to lag a server," the top results are often advertisements from the police or Europol. These ads lead to landing pages that explain the illegality of DDoS attacks and the potential for prison sentences, fines, and the permanent loss of digital equipment.
Furthermore, authorities have successfully removed over 100 URLs from search results that previously promoted these illegal services. By making the services harder to find, law enforcement aims to raise the barrier to entry for casual users. Perhaps the most sophisticated intervention involves "on-chain" warning messages. By tracking cryptocurrency payments made to booter service operators, authorities are now able to attach warning messages to the blockchain transactions themselves. When a user attempts to pay for an attack, they may receive a notification that their transaction is being monitored by law enforcement.
International Synergy and Official Responses
The success of Operation PowerOFF is largely attributed to the unprecedented level of cooperation between 21 participating nations. Cybercrime is inherently borderless; a user in Japan can pay for a service hosted in the Netherlands to attack a target in the United States. Only through a unified legal and technical framework can such a network be dismantled.
In a statement following the action week, Europol emphasized the importance of high-value target (HVT) identification. By focusing on the most prolific users and the developers behind the attack scripts, law enforcement can have a disproportionate impact on the overall volume of global DDoS traffic. Officials from the FBI and the UK’s National Crime Agency have echoed these sentiments, noting that the intelligence gathered from the 53 seized domains will likely fuel investigations for years to come.
"The illegal use of DDoS-for-hire services is not a victimless crime," noted one senior official involved in the operation. "It causes massive financial loss to businesses, disrupts essential public services, and can even put lives at risk when emergency communication systems are targeted. We are committed to ensuring that those who facilitate or use these services face the full force of the law."
Broader Impact and the Future of Network Security
The implications of Operation PowerOFF extend beyond the immediate arrests and domain seizures. This operation has provided researchers and cybersecurity professionals with invaluable insights into the "supply chain" of DDoS attacks. By analyzing the seized infrastructure, experts can better understand the types of vulnerabilities being exploited in IoT devices, leading to better security standards and patch management across the industry.
However, the battle is far from over. As law enforcement shuts down booter services, cybercriminals are increasingly turning to "darknet" forums and encrypted messaging apps like Telegram to coordinate attacks. The rise of decentralized and peer-to-peer (P2P) botnets also presents a new challenge, as there is no central server for authorities to seize.
Despite these challenges, the latest results of Operation PowerOFF demonstrate that the "low-risk, high-reward" nature of DDoS attacks is shifting. With 75,000 users now aware that they are being watched and the infrastructure of 53 major platforms in the hands of the police, the cost of engaging in this type of cybercrime has risen significantly. The move toward awareness campaigns and search engine disruption represents a holistic approach to cybercrime—one that addresses not just the technology, but the human element that drives it. As the operation enters its next phase, the focus will remain on persistent disruption, ensuring that those who seek to "power off" the internet find themselves the targets of a much more powerful and permanent shutdown.