CISA Urges Immediate Action as Palo Alto Networks Firewalls Face Active Exploitation via Reflected DoS Vulnerability

The Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent directive to federal agencies and private sector partners, warning that a high-severity vulnerability in Palo Alto Networks’ PAN-OS software is being actively exploited in the wild. The flaw, tracked as CVE-2022-0028, allows unauthenticated remote attackers to weaponize enterprise firewalls to launch massive reflected and amplified denial-of-service (DoS) attacks. Following evidence of active exploitation, CISA has added the bug to its Known Exploited Vulnerabilities (KEV) catalog, mandating that federal civilian executive branch agencies apply the necessary patches by September 9 to mitigate the risk of disruption to critical services.
The vulnerability stems from a specific misconfiguration in the PAN-OS URL filtering policy. When certain conditions are met, the firewall can be coerced into participating in a Distributed Denial of Service (DDoS) campaign, where the firewall itself becomes the source of the attack traffic. While Palo Alto Networks initially characterized the flaw as affecting only a limited number of non-standard configurations, the transition of the bug into the KEV catalog signals a heightened level of risk that necessitates immediate remediation across the global cybersecurity landscape.
Technical Analysis of CVE-2022-0028
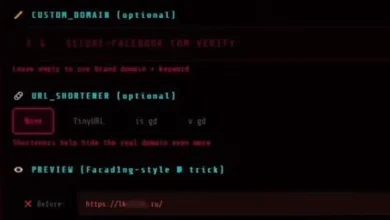
At its core, CVE-2022-0028 is a vulnerability involving the improper handling of network traffic when a URL filtering profile is incorrectly applied. Palo Alto Networks’ PA-Series, VM-Series, and CN-Series devices utilize PAN-OS to manage complex security rules. The flaw manifests when a firewall configuration includes a URL filtering profile with one or more blocked categories assigned to a security rule that has a source zone containing an external-facing network interface.
Under these specific circumstances, an attacker can send a spoofed TCP packet to the firewall. Because the source IP address of the packet is spoofed to match that of a target victim, the firewall—attempting to enforce its filtering policy—responds to the victim instead of the attacker. This creates a "reflection" effect. Furthermore, because of the way the firewall handles these packets, the response is significantly larger than the initial request, leading to "amplification."
In a typical TCP-based Reflected Denial-of-Service (RDoS) attack, the adversary sends a SYN packet with a spoofed source IP. The firewall responds with a SYN-ACK packet to the victim. If the victim does not acknowledge the packet, the firewall may continue to retransmit the SYN-ACK multiple times. This process exhausts the bandwidth and processing power of the target, potentially knocking websites, servers, or entire networks offline.
Scope of Affected Products and Necessary Patches
The vulnerability impacts a wide range of PAN-OS versions across various hardware and software platforms. Palo Alto Networks has released comprehensive patches and urges administrators to verify their current versioning immediately. The following versions are identified as vulnerable:
- PAN-OS versions prior to 10.2.2-h2
- PAN-OS versions prior to 10.1.6-h6
- PAN-OS versions prior to 10.0.11-h1
- PAN-OS versions prior to 9.1.14-h4
- PAN-OS versions prior to 9.0.16-h3
- PAN-OS versions prior to 8.1.23-h1
Palo Alto Networks has clarified that the vulnerability does not impact PAN-OS 11.0 or later versions, as the underlying logic was restructured in newer releases. However, for organizations running legacy hardware or specific virtualized environments, the threat remains potent until the specific "h" (hotfix) updates are applied.
The CISA Mandate and Binding Operational Directive 22-01
The inclusion of CVE-2022-0028 in the CISA KEV catalog is a significant escalation. Under Binding Operational Directive (BOD) 22-01, "Reducing the Significant Risk of Known Exploited Vulnerabilities," federal agencies are legally required to remediate vulnerabilities listed in the catalog within a specific timeframe. For this particular Palo Alto Networks flaw, the deadline is set for September 9.
While CISA’s mandate technically applies only to federal agencies, the KEV catalog serves as a "gold standard" for private sector organizations and local governments. Security experts widely recommend that any vulnerability added to this list be prioritized for patching within 24 to 48 hours, regardless of whether the organization is a federal entity. The KEV catalog is curated based on clear evidence of active exploitation, meaning that hackers are already using this specific method to bypass or abuse security infrastructure.
Understanding the RDoS Landscape
Reflected and amplified DoS attacks have become a preferred weapon for both hacktivists and state-sponsored actors due to their efficiency. Traditionally, DDoS attacks required a massive botnet of compromised "zombie" computers to overwhelm a target. In contrast, RDoS attacks allow a single attacker with relatively modest resources to leverage the high-bandwidth connections of legitimate infrastructure—such as enterprise-grade firewalls—to do the heavy lifting.
Data from cybersecurity firms indicates that the peak size of volumetric attacks has grown exponentially over the last five years. Attackers have historically exploited protocols like DNS, NTP, and Memcached for amplification. The discovery that a mainstream security product like PAN-OS can be used as an amplification vector is particularly concerning, as firewalls are typically positioned at the edge of a network with access to high-capacity internet uplinks.
In the case of CVE-2022-0028, the amplification factor depends on the number of SYN-ACK retransmits configured or hardcoded into the reflection service. Even a modest amplification factor can be devastating when multiplied across thousands of vulnerable firewalls.
Timeline and Chronology of the Event
The timeline of CVE-2022-0028 highlights the transition from a discovered misconfiguration to an actively exploited threat:
- Early August: Palo Alto Networks identifies a potential issue where URL filtering policies could be abused. Initial internal investigations suggest the configuration is non-standard and likely unintended by administrators.
- Mid-August: Palo Alto Networks issues an initial advisory and begins rolling out hotfixes for various PAN-OS branches. The company notes that it has received reports of "attempted exploitation" in the wild.
- Late August: Reports from threat intelligence sources indicate that the vulnerability is being used in actual RDoS campaigns, prompting a re-evaluation of the risk level.
- August 22: CISA officially adds CVE-2022-0028 to the KEV catalog, citing evidence of active exploitation.
- September 9 Deadline: The date by which all U.S. federal agencies must have confirmed the application of patches or the removal of the vulnerable configurations.
Official Responses and Remediation Best Practices
Palo Alto Networks has been proactive in its communication, stating that while the vulnerability is high-severity, it requires a very specific set of circumstances to be exploitable. "A PAN-OS URL filtering policy misconfiguration could allow a network-based attacker to conduct reflected and amplified TCP denial-of-service attacks," the company noted in its technical advisory. The company further emphasized that "the configuration is likely unintended by the network administrator," suggesting that a review of security rules may reveal if a system is at risk even before a patch is applied.
For organizations unable to patch immediately, Palo Alto Networks and CISA suggest the following mitigation steps:
- Configuration Review: Ensure that no URL filtering profiles with blocked categories are applied to security rules with a source zone that includes an external-facing interface.
- Packet Filtering: Implement upstream filtering to block spoofed traffic where possible.
- Monitoring: Use network monitoring tools to look for unusual spikes in outbound SYN-ACK traffic, which may indicate that a firewall is being used as a reflector.
Broader Implications for Cybersecurity
The exploitation of CVE-2022-0028 underscores a growing trend where the very tools designed to protect a network are turned against it. Firewalls, load balancers, and VPN gateways are increasingly targeted not just for data breaches, but as infrastructure for broader attacks.
This incident also highlights the complexity of modern network security software. A seemingly minor interaction between a URL filtering policy and a source zone configuration can create a global security risk. As organizations move toward Zero Trust architectures, the reliance on edge firewalls remains high, making their integrity paramount.
Furthermore, the involvement of CISA illustrates the agency’s evolving role as a proactive shield for the nation’s digital infrastructure. By shortening the window between the discovery of exploitation and the mandatory patching deadline, CISA is attempting to close the "vulnerability gap" that attackers frequently exploit.
As the September 9 deadline approaches, the cybersecurity community will be watching closely to see if the volume of RDoS attacks leveraging PAN-OS decreases. For now, the message from both the vendor and the government is clear: the threat is real, the exploitation is active, and the time to patch is now. Organizations that fail to act risk not only their own availability but also becoming an unwitting participant in attacks against others.