Starkiller Phishing-as-a-Service Leverages Reverse Proxies and Real-Time Session Monitoring to Neutralize Multi-Factor Authentication
The landscape of cyber-enabled fraud is undergoing a sophisticated transformation as threat actors move away from static, easily detectable phishing templates toward dynamic, live-relay architectures. Historically, phishing campaigns relied on "kits" that hosted static replicas of popular login pages, such as those for Microsoft 365, Google, or Facebook. While effective against the unwary, these static sites were prone to rapid detection by security researchers and automated scanners that flagged suspicious domain registrations or mismatched HTML code. However, a new Phishing-as-a-Service (PhaaS) platform dubbed Starkiller has emerged, representing a significant evolution in the commoditization of high-end cybercrime. By utilizing a "man-in-the-middle" (MitM) or "adversary-in-the-middle" (AitM) approach, Starkiller allows even low-skill attackers to bypass modern security protocols, including multi-factor authentication (MFA), by acting as a real-time bridge between the victim and the legitimate service provider.
The Technical Architecture of Starkiller
According to a detailed technical analysis released by the security firm Abnormal AI, Starkiller distinguishes itself from traditional phishing kits through its use of containerization and headless browser technology. When a prospective attacker selects a brand to target, the Starkiller infrastructure spins up a dedicated Docker container. This container runs an instance of headless Chrome—a web browser without a graphical user interface—that navigates to the actual, legitimate login page of the target brand, such as Apple, Microsoft, or a major financial institution.
Instead of presenting the user with a pre-built fake page, Starkiller serves as a reverse proxy. It fetches the live content from the real website and relays it to the victim’s browser. This means that the victim is interacting with the genuine login interface, including all its interactive elements, security images, and localized language settings. As the victim types their username and password, the Starkiller infrastructure captures these keystrokes in real-time while simultaneously forwarding them to the legitimate site’s servers.
The most critical component of this architecture is its ability to handle Multi-Factor Authentication (MFA). Because the service is proxying the live session, when the legitimate site prompts the user for a one-time password (OTP), a push notification, or a hardware key response, the Starkiller relay passes that prompt through to the victim. Once the victim provides the MFA credential, it is forwarded to the real site to complete the authentication. The attacker then intercepts the resulting session cookies and authentication tokens. These tokens allow the attacker to maintain persistent access to the victim’s account without needing to know the password or bypass the MFA a second time, effectively rendering traditional two-step verification moot.
Deceptive URL Masking and the "At-Sign" Trick
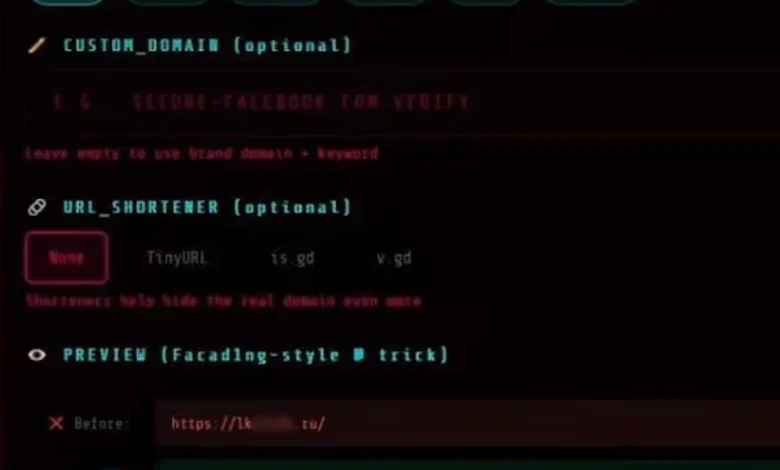
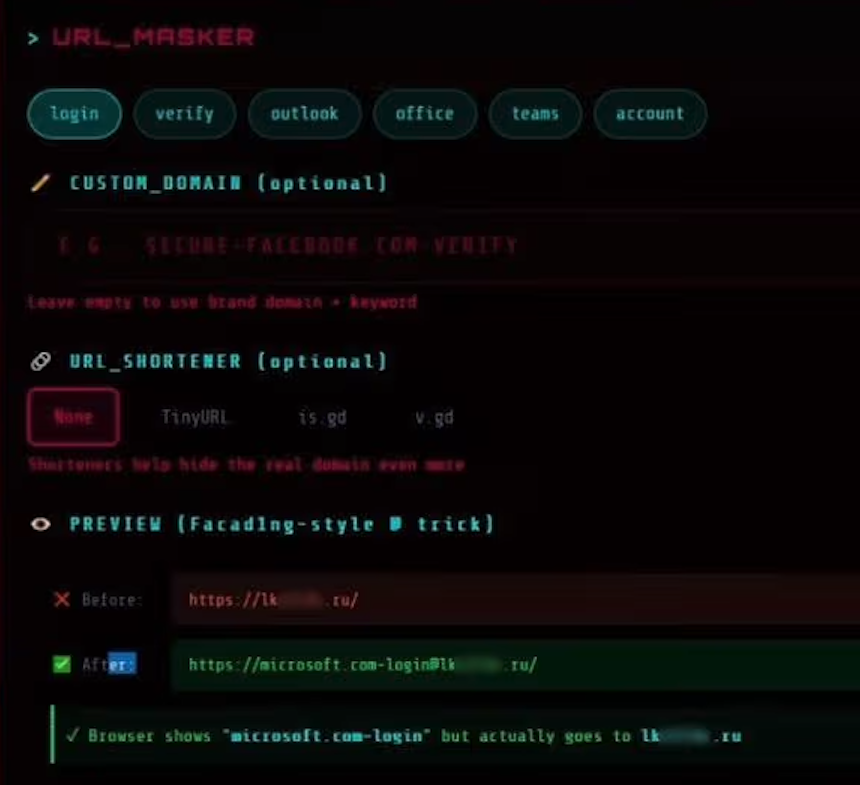
A primary hurdle for any phishing campaign is the URL. Security-conscious users are often taught to inspect the address bar for discrepancies. Starkiller addresses this by employing a sophisticated "URL Masker" feature that utilizes an old but effective URI (Uniform Resource Identifier) syntax trick involving the "@" symbol.
In standard web protocols (RFC 3986), the portion of a URL appearing before an "@" symbol is technically treated as "user information" or credentials intended for the server. For example, in a URL structured as https://[email protected], many modern browsers and unsuspecting users may only focus on the first part of the string—login.microsoft.com—assuming it is the destination. In reality, the browser ignores the prefix and navigates to the domain following the "@" sign.
Starkiller’s interface allows its "subscribers" to generate these deceptive links with ease, often combining them with URL shorteners to further obscure the final destination. This tactic is specifically designed to defeat automated email filters that look for known malicious domains while simultaneously tricking human observers who have been trained to look for specific keywords in the subdomain.
The Commoditization of Cybercrime via Jinkusu
Starkiller is not an isolated tool but part of a broader ecosystem managed by a threat group calling itself Jinkusu. This group operates Starkiller as a "SaaS" (Software-as-a-Service) model, providing a professional-grade user experience for cybercriminals. The platform includes a comprehensive dashboard that mirrors the analytics tools used by legitimate marketing firms.
Within the Jinkusu interface, operators can track:
- Real-time Session Monitoring: Attackers can "live-stream" the victim’s screen, watching as they enter data and navigate the site.
- Keylogger Integration: Every individual keystroke is logged, ensuring that even if a session times out, the credentials are saved.
- Geo-Tracking: The service identifies the physical location and IP address of the victim, allowing attackers to tailor their follow-up actions based on the victim’s jurisdiction.
- Automated Alerts: The platform integrates with Telegram, sending instant notifications to the attacker’s mobile device the moment a new set of credentials or a session token is successfully harvested.
Furthermore, the Jinkusu group maintains an active community forum where "customers" can request new features, troubleshoot deployment issues, and share successful phishing templates. One notable "a-la-carte" feature offered by the group is a tool that automatically scrapes contact lists and email addresses from compromised accounts. This data is then used to fuel secondary phishing waves, creating a self-sustaining cycle of exploitation.
Chronology and Evolution of Phishing Tactics
The emergence of Starkiller represents the "third wave" of phishing evolution. To understand its impact, one must look at the historical progression of these attacks:
- Phishing 1.0 (Static Templates): Early 2000s to mid-2010s. Attackers sent mass emails with links to static HTML pages. These were easy to host but also easy to block via domain blacklisting and signature-based detection.
- Phishing 2.0 (Automated Kits and Obfuscation): Mid-2010s to 2020. Kits became more automated, using JavaScript obfuscation to hide the source code from scanners. MFA began to pose a significant challenge to these methods.
- Phishing 3.0 (Adversary-in-the-Middle): 2021 to Present. Tools like Evilginx2 and now Starkiller moved toward proxying live traffic. This shift was a direct response to the widespread adoption of MFA. As enterprises strengthened their perimeters, attackers shifted their focus to hijacking the authenticated session itself rather than just the credentials.
Abnormal AI researchers Callie Baron and Piotr Wojtyla noted that Starkiller represents a democratization of these advanced "3.0" tactics. Previously, setting up a reverse proxy for phishing required significant technical expertise in server configuration and network protocols. Starkiller removes these barriers, allowing "script kiddies" and low-level fraudsters to execute enterprise-grade attacks for a subscription fee.
Industry Implications and Data on Phishing Trends
The rise of platforms like Starkiller aligns with broader industry data regarding the failure of traditional MFA. According to the 2024 Verizon Data Breach Investigations Report (DBIR), "credentials" remain the primary entry point for breaches, involved in nearly 38% of all incidents. Furthermore, the Anti-Phishing Working Group (APWG) reported a record-breaking number of phishing attacks in recent years, with a notable shift toward targeting enterprise SaaS and webmail providers.
Security experts argue that the success of Starkiller highlights a critical vulnerability in "phishable" MFA, such as SMS-based codes or standard push notifications. Because these methods rely on a user entering a code into a web form, they are inherently susceptible to relay attacks. In contrast, "unphishable" MFA—such as FIDO2-compliant hardware keys or Windows Hello—utilizes a cryptographic handshake between the hardware and the specific, legitimate domain. Because the domain in a Starkiller attack (e.g., the .ru domain hidden after the @) does not match the legitimate domain stored in the hardware key, the authentication attempt would fail.
Analysis of the Broader Impact
The deployment of Starkiller by the Jinkusu group signals a dangerous trend in the "professionalization" of the dark web. By offering features like campaign analytics and conversion rate tracking, the developers are treating cybercrime as a legitimate business enterprise. This lowers the "cost of doing business" for criminals, as they no longer need to spend hours configuring infrastructure; they can simply "rent" a high-performance attack platform.
From a defensive standpoint, the emergence of Starkiller renders many traditional security awareness training modules obsolete. Users are often taught to "check the lock icon" or "look for the correct logo," both of which are present in a Starkiller attack because the victim is seeing the real site. This necessitates a shift in corporate defense strategies toward:
- FIDO2/WebAuthn Adoption: Moving away from OTPs and push notifications toward hardware-backed authentication that is bound to the origin domain.
- Behavioral AI Detection: Utilizing security tools that can identify the subtle network latency and traffic patterns associated with reverse proxies and Docker-based relays.
- Enhanced Email Security: Implementing advanced threat protection (ATP) that can "sandbox" and follow links to their final destination, looking past URL masking tricks.
As the Jinkusu group continues to refine its offerings, the security community expects a surge in AitM attacks. The ease of use provided by Starkiller ensures that the "barrier to entry" for sophisticated account takeover (ATO) fraud has never been lower. For organizations, the message is clear: traditional MFA is no longer a silver bullet, and the evolution of phishing infrastructure requires an equally rapid evolution in defensive architecture.








