Global Law Enforcement Dismantles Major DDoS-for-Hire Infrastructure in Operation PowerOFF

In a sweeping international effort to curb the rising tide of automated cyberattacks, law enforcement agencies from 21 countries have successfully executed a coordinated strike against the world’s most prominent distributed denial-of-service (DDoS) for-hire platforms. The multi-phased initiative, known as Operation PowerOFF, resulted in the seizure of 53 web domains, the arrest of four key individuals, and the acquisition of massive databases containing information on more than 3 million criminal user accounts. This operation represents one of the most significant blows to the "booter" service ecosystem to date, targeting the technical infrastructure that has long allowed even novice actors to launch devastating digital attacks against global targets.
The operation was spearheaded by Europol’s European Cybercrime Centre (EC3) and the Joint Cybercrime Action Taskforce (J-CAT), with critical support from the U.S. Federal Bureau of Investigation (FBI) and the Department of Justice (DoJ). By dismantling the digital architecture of these services, authorities have not only halted ongoing attacks but have also gathered a treasure trove of intelligence that will likely fuel investigations for years to come. The crackdown targeted "booter" or "stresser" services—commercial entities that offer DDoS attacks as a subscription-based product, effectively democratizing cybercrime by providing high-powered disruptive tools to anyone with a credit card or cryptocurrency wallet.
The Scope of Operation PowerOFF
Operation PowerOFF is an ongoing, long-term international effort designed to dismantle the business model of DDoS-for-hire services. The latest phase of the operation saw a massive mobilization of law enforcement resources across four continents. Participating nations included Australia, Austria, Belgium, Brazil, Bulgaria, Denmark, Estonia, Finland, Germany, Japan, Latvia, Lithuania, Luxembourg, the Netherlands, Poland, Portugal, Sweden, Thailand, the United Kingdom, and the United States.
According to Europol, the seized infrastructure included servers, databases, and administrative backends that powered the DDoS attacks. By gaining access to these systems, investigators were able to identify approximately 75,000 unique users who had actively engaged with these platforms to facilitate criminal activity. In addition to the four arrests made during this phase, authorities executed 25 search warrants globally, signaling that the investigation is far from over.

The seizure of databases containing 3 million user accounts is particularly significant. These records often include IP addresses, email addresses, payment information, and logs of targeted attacks. Law enforcement agencies have already begun a proactive campaign to contact these users. In many jurisdictions, authorities are sending formal warning letters or emails to individuals identified in the databases, informing them that their activities have been recorded and that they are under scrutiny. This "nudge" strategy aims to deter young or first-time offenders who may not fully grasp the legal consequences of using booter services.
Understanding the DDoS-for-Hire Ecosystem
DDoS attacks work by overwhelming a target website, server, or network with a massive volume of "junk" internet traffic. This flood of data consumes the target’s bandwidth and processing power, leading to significant performance degradation or a total service outage. While large-scale DDoS attacks were once the province of highly skilled hackers or state-sponsored groups, the emergence of the "booter" industry has fundamentally changed the threat landscape.
Booter services are typically marketed as legitimate "network stress-testing tools" for administrators to check their own infrastructure’s resilience. However, this is largely a legal smokescreen. In practice, these platforms are designed to launch malicious attacks against third parties. They offer user-friendly interfaces, tiered pricing models, and even customer support, making them accessible to individuals with zero technical proficiency.
The motivations behind these attacks are diverse. In many cases, they are driven by financial gain through extortion, where a criminal demands payment to stop the attack. In others, the motive is competitive disruption—attacking a rival gaming server or business. Furthermore, hacktivism remains a primary driver, with individuals using DDoS as a form of digital protest against government agencies or corporations. Europol noted that the low cost of these services—sometimes as little as $10 for a single attack—makes them a prolific and dangerous entry point for aspiring cybercriminals.

The United States’ Strategic Response and IoT Botnet Seizures
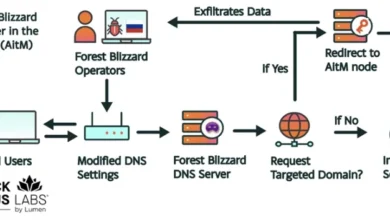
Parallel to the broader Europol-led effort, the U.S. Department of Justice (DoJ) and the FBI announced specific actions targeting the Internet of Things (IoT) botnets that often provide the "firepower" for booter services. In many cases, booter platforms do not own their own massive server farms; instead, they rent or control botnets—networks of compromised devices like smart cameras, routers, and DVRs—to generate the necessary traffic for an attack.
The DoJ revealed that court-authorized operations had successfully disrupted several leading DDoS-for-hire domains, including "Vac Stresser" and "Mythical Stress." These specific platforms were responsible for thousands of attacks daily. Visitors to these sites are now greeted with a stark law enforcement seizure banner. The banner serves as a public service announcement, stating: "DDoS attacks are illegal. Anyone operating or utilizing DDoS services is subject to investigation, prosecution, and other law enforcement action."
The FBI has also launched a targeted digital advertising campaign. When individuals in certain regions search for DDoS-related terms on major search engines, they are presented with advertisements warning them of the illegality of such services. This proactive approach is part of a broader shift in law enforcement strategy: moving beyond just making arrests to actively disrupting the supply and demand of the cybercrime market.
A History of Enforcement: The Evolution of PowerOFF
Operation PowerOFF is not a one-time event but part of a sustained strategy that has been evolving for years. In December 2022, a similar phase of the operation resulted in the seizure of 48 domains and charges against several administrators. More recently, in August 2025, U.S. authorities dismantled the "RapperBot" botnet, which had been used to target victims in over 80 countries since 2021.

The continuity of Operation PowerOFF demonstrates the persistence of law enforcement. As soon as one booter service is taken down, others often emerge to fill the vacuum. By repeatedly seizing domains and databases, authorities increase the risk for both providers and users. The goal is to make the DDoS-for-hire market so volatile and risky that it becomes unattractive to potential customers and unprofitable for operators.
Technical Mechanics: How Booter Services Exploit the Internet
The technical sophistication of these services varies, but they often utilize "reflection" and "amplification" techniques to maximize their impact. In a reflection attack, the criminal sends a small request to a legitimate third-party server (like a DNS or NTP server), spoofing the IP address of the victim. The third-party server then sends a much larger response to the victim’s IP address. This allows an attacker to "amplify" their relatively small amount of bandwidth into a massive flood of traffic.
Furthermore, the proliferation of insecure IoT devices has provided a nearly inexhaustible supply of "bots" for these networks. Because many IoT devices have weak default passwords and are rarely patched, they are easily compromised by malware like Mirai or its successors. Once infected, these devices can be commanded remotely to participate in a DDoS attack, often without the owner ever knowing their device has been weaponized.
The Psychology of Deterrence and Global Impact
One of the most innovative aspects of the current phase of Operation PowerOFF is the focus on the "human element" of cybercrime. By obtaining the database of 3 million accounts, law enforcement has effectively stripped away the anonymity that users of these services rely on.

For many young individuals, launching a DDoS attack feels like a victimless prank or a consequence-free way to gain status in online communities. By sending warning letters and placing seizure banners, law enforcement is breaking that illusion. The message is clear: the police know who you are, they know what you did, and there is a digital paper trail connecting you to a criminal enterprise.
The broader implications for global cybersecurity are significant. DDoS attacks are often used as a precursor or a distraction for more serious intrusions, such as ransomware deployment or data exfiltration. By reducing the availability of DDoS-for-hire tools, authorities are indirectly protecting the integrity of global financial systems, healthcare providers, and government infrastructure.
Conclusion: The Ongoing Battle Against Automated Cybercrime
While the takedown of 53 domains is a major victory, experts warn that the threat of DDoS attacks remains persistent. The decentralized nature of the internet and the constant influx of new, insecure devices mean that the infrastructure for these attacks can be rebuilt. However, the success of Operation PowerOFF proves that international cooperation is the most effective weapon in the law enforcement arsenal.
The 21 nations involved in this operation have sent a powerful message to the global cybercrime community. The era of consequence-free "booting" is coming to an end. As authorities continue to analyze the seized data and track down the individuals behind the 3 million accounts, the ripple effects of this operation will be felt for years to come. Organizations are encouraged to remain vigilant, implement robust DDoS mitigation strategies, and report any incidents to local law enforcement to help build future cases against these digital predators.