Microsoft Patch Tuesday April 2026 Record Breaking 167 Security Vulnerabilities Fixed Amid AI Driven Bug Discovery Surge
The global cybersecurity landscape faced a significant test this week as Microsoft released its April 2026 security update, addressing a staggering 167 vulnerabilities across its Windows operating systems and associated software suite. This release marks one of the largest single-day patch deployments in the company’s history, highlighted by the remediation of a critical zero-day exploit in Microsoft SharePoint Server and a highly publicized privilege escalation flaw in Windows Defender known as "BlueHammer." The surge in reported vulnerabilities, which includes nearly 60 browser-related fixes, has ignited a broader industry discussion regarding the role of artificial intelligence in accelerating the discovery of software weaknesses.
Beyond the Microsoft ecosystem, the security window for April has been particularly volatile. Google Chrome recently addressed its fourth zero-day vulnerability of 2026, while Adobe issued an emergency out-of-band update for Acrobat and Reader to neutralize an actively exploited flaw capable of remote code execution. Security analysts suggest that the sheer volume of patches this month reflects a "new normal" in the digital arms race, where both defenders and threat actors leverage advanced automation to scan codebases at unprecedented speeds.
Critical Zero-Day Threats: SharePoint and Windows Defender
At the forefront of the April update is CVE-2026-32201, a vulnerability in Microsoft SharePoint Server that attackers are already actively exploiting in the wild. This flaw allows unauthorized actors to perform spoofing attacks, essentially enabling them to manipulate or falsify trusted content within an organization’s SharePoint environment. Because SharePoint serves as a central repository for internal communications, document management, and collaborative workflows, the ability to spoof content poses a severe risk to corporate integrity.
Mike Walters, president and co-founder of Action1, emphasized the psychological and operational dangers of this specific vulnerability. According to Walters, CVE-2026-32201 can be weaponized to deceive employees or partners by presenting fraudulent data as legitimate corporate guidance. This can facilitate highly effective phishing campaigns or social engineering efforts that lead to credential theft and deeper network penetration. The active exploitation of this bug signifies that state-sponsored or sophisticated criminal groups have already integrated it into their playbooks, making immediate patching a non-negotiable priority for enterprise IT departments.
Simultaneously, Microsoft addressed CVE-2026-33825, a vulnerability in Windows Defender dubbed "BlueHammer." Unlike many flaws discovered through private bug bounty programs, BlueHammer became a public relations and security challenge after a researcher, reportedly frustrated by Microsoft’s initial response to their report, leaked the exploit code online. The flaw allows for privilege escalation, a process where a low-level user or a piece of malware gains administrative or "system" level permissions on a machine. Will Dormann, a senior principal vulnerability analyst at Tharros, confirmed following the update that the publicly available exploit code no longer functions on patched systems, providing relief to administrators who feared a wave of automated attacks utilizing the leaked script.
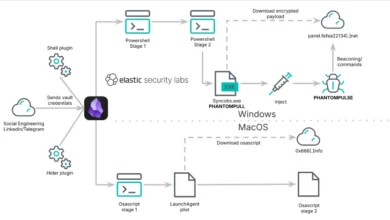
The AI Factor: Project Glasswing and the Vulnerability Surge
The sheer volume of the April update—nearly 170 patches—has led many industry experts to look toward the horizon of artificial intelligence. Adam Barnett, lead software engineer at Rapid7, noted that this month’s total is a record-breaking figure, largely bolstered by browser vulnerabilities. Barnett and other analysts have pointed to the recent announcement of "Project Glasswing" by Anthropic. While Project Glasswing remains unreleased to the general public, reports suggest the AI model possesses advanced capabilities for identifying deep-seated logic flaws and memory corruption issues in complex software architectures.
The correlation between the rise of high-capability AI models and the spike in CVE (Common Vulnerabilities and Exposures) reporting is becoming harder to ignore. "A safe conclusion is that this increase in volume is driven by ever-expanding AI capabilities," Barnett stated. He predicted that as AI tools become more available to both independent researchers and corporate security teams, the volume of vulnerability reporting will continue to escalate. This creates a dual-edged sword: while more bugs are being found and fixed, the burden on IT departments to test and deploy patches at this scale is reaching a breaking point.
The integration of Chromium-based engines into Microsoft Edge also contributes to these numbers. Because Edge shares a core architecture with Google Chrome, any vulnerability discovered in the Chromium project must be addressed by Microsoft as well. This month, the Chromium maintainers acknowledged a vast array of researchers, many of whom are suspected of using proprietary AI scanning tools to audit the open-source code.
Adobe and Google: Emergency Responses in a High-Stakes Month
While Microsoft’s Patch Tuesday is a scheduled event, other vendors were forced into emergency action this month. Adobe released a critical update (CVE-2026-34621) for Adobe Acrobat and Reader on April 11, following evidence of active exploitation. Satnam Narang, a senior staff research engineer at Tenable, pointed out a troubling detail regarding this flaw: indications suggest that threat actors may have been utilizing this zero-day in targeted attacks since at least November 2025.
The Adobe flaw allows for remote code execution (RCE), meaning an attacker could take full control of a victim’s system simply by tricking them into opening a malicious PDF file. The five-month gap between the suspected first use of the exploit and the issuance of a patch highlights the persistent challenge of "invisible" zero-days that circulate in the dark web or are held by advanced persistent threat (APT) groups before they are caught by automated telemetry.
Google Chrome also faced a significant hurdle, patching CVE-2026-5281, its fourth zero-day of the year. This high-severity flaw was part of a larger update that addressed 21 security holes. For end-users, these browser vulnerabilities represent the most immediate threat, as they are often exploited through "drive-by" downloads or malicious advertisements (malvertising) on otherwise legitimate websites.
Chronology of the April 2026 Security Cycle
The timeline of the April security events illustrates a period of intense activity for the global cybersecurity community:
- November 2025 (Retrospective): Earliest suspected exploitation of the Adobe Acrobat RCE vulnerability (CVE-2026-34621) begins in targeted attacks.
- Late March 2026: Researchers report the "BlueHammer" Windows Defender flaw to Microsoft.
- April 3, 2026: Google releases a major Chrome update to address CVE-2026-5281 and 20 other vulnerabilities.
- April 7, 2026: Anthropic announces Project Glasswing, sparking industry-wide debate on AI-driven vulnerability discovery.
- April 9, 2026: A disgruntled researcher leaks the "BlueHammer" exploit code on public repositories after a dispute with Microsoft over the severity of the bug.
- April 11, 2026: Adobe issues an emergency out-of-band patch for Acrobat and Reader to stop active exploitation of CVE-2026-34621.
- April 14, 2026 (Patch Tuesday): Microsoft releases updates for 167 vulnerabilities, including the SharePoint zero-day (CVE-2026-32201) and the official fix for BlueHammer.
Impact on Enterprise Operations and "Patch Fatigue"
The logistical challenge of managing 167 patches in a single cycle cannot be overstated. For large enterprises, every patch must be tested against internal applications to ensure that security fixes do not "break" critical business software. When the volume of patches reaches these heights, the window between the release of a patch and the development of a functional exploit by hackers—often referred to as the "mean time to exploit"—shrinks significantly.
Satnam Narang of Tenable noted that April 2026 has become the second-biggest Patch Tuesday in history. This volume creates a phenomenon known as "patch fatigue," where IT administrators are overwhelmed by the sheer number of critical updates. The danger of patch fatigue is that administrators might delay deployments, inadvertently leaving the door open for attackers who use the patch itself as a blueprint to create exploits for unpatched systems (a process known as "1-day" exploitation).
To mitigate this, security experts recommend a prioritized approach. For the April cycle, the priority list is clear:
- SharePoint Server (CVE-2026-32201): Due to active exploitation and the risk of internal spoofing.
- Windows Defender (CVE-2026-33825): Due to the public availability of exploit code.
- Browsers (Chrome and Edge): Due to the high frequency of user interaction with untrusted web content.
- Adobe Acrobat/Reader: Especially for departments that handle high volumes of external documents, such as legal or HR.
Looking Forward: The Future of Defensive AI
As the dust settles on this record-breaking Patch Tuesday, the conversation has shifted to how organizations can adapt to an environment where software flaws are discovered at an exponential rate. The consensus among analysts is that if AI is being used to find bugs, AI must also be used to fix them and monitor for their exploitation.
The emergence of tools like Project Glasswing suggests that the days of manual, human-only code audits are ending. While this may lead to more "noisy" months with high CVE counts, it ultimately results in a more resilient software ecosystem. However, the transition period remains perilous. As seen with the BlueHammer incident, the human element—researcher ethics, vendor responsiveness, and administrative diligence—remains the most volatile variable in the cybersecurity equation.
For individual users, the advice remains simple but vital: enable automatic updates and restart applications regularly. As Google and Microsoft have both noted, a patch is only effective once the software is restarted to load the new, secure code. In an era of record-breaking vulnerability counts, the simple act of a system reboot has become a critical component of national and corporate security.