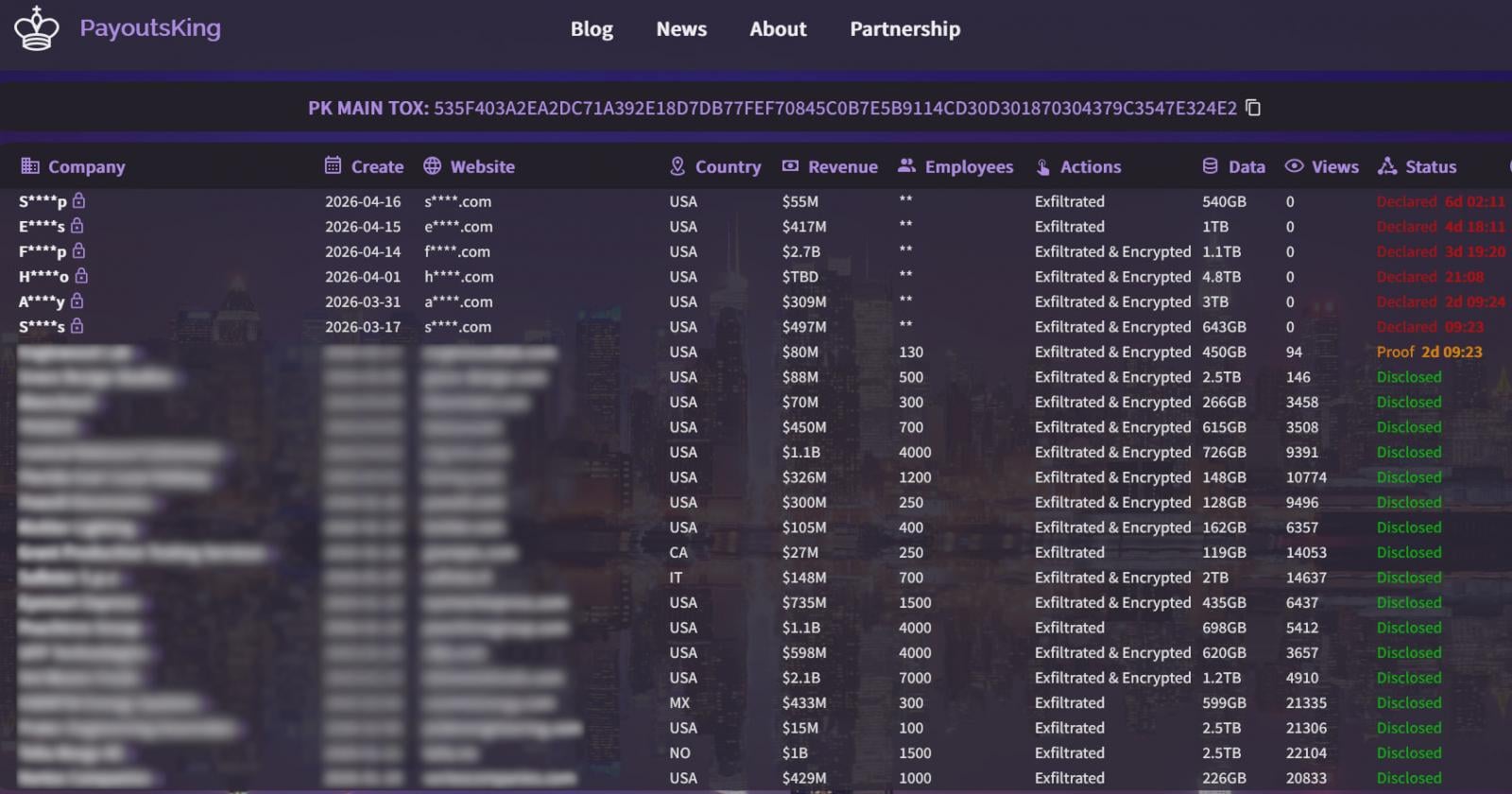
Payouts King Ransomware Leverages QEMU Virtual Machines to Evade Endpoint Detection and Establish Stealthy Network Backdoors

The cybersecurity landscape is witnessing a sophisticated evolution in ransomware delivery mechanisms, as threat actors increasingly turn to legitimate virtualization tools to mask their activities. Recent investigations by security researchers have identified a growing trend where the Payouts King ransomware group utilizes the QEMU (Quick Emulator) platform to create "black box" environments on compromised systems. By nesting a malicious operating system within a virtual machine (VM) on a target host, these attackers are effectively bypassing traditional Endpoint Detection and Response (EDR) solutions, which often lack the visibility required to inspect processes running inside a virtualized guest environment.
QEMU, an open-source hosted hypervisor that performs hardware virtualization and CPU emulation, has long been a staple tool for system administrators and developers. However, its ability to run diverse operating systems with minimal overhead makes it an ideal vehicle for cybercriminals. When deployed as a reverse SSH backdoor, QEMU allows attackers to establish persistent, encrypted tunnels between the victim’s internal network and the attacker’s command-and-control (C2) infrastructure. Because the security software on the host machine typically monitors the host’s own kernel and user-space processes, the activities occurring within the QEMU guest—such as scanning the local network, harvesting credentials, or staging data for exfiltration—remain largely invisible.
The Emergence of Virtualization as an Evasion Tactic
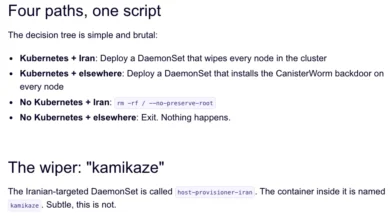
The abuse of virtualization is not an entirely new phenomenon, but its integration into the standard operating procedures of high-profile ransomware groups marks a significant escalation. Historically, threat actors such as the 3AM ransomware group and the operators behind the LoudMiner cryptomining campaign have leveraged similar tactics. The "CRON#TRAP" phishing campaign also utilized backdoored Linux VMs to establish a foothold in Windows environments. The adoption of this method by Payouts King, a relatively new but aggressive player in the extortion space, suggests that the technique has reached a level of maturity and reliability that appeals to sophisticated financial motivated groups.
By running a lightweight version of Linux, such as Alpine Linux, inside the QEMU emulator, attackers can deploy a comprehensive suite of penetration testing and data exfiltration tools without triggering the signature-based or heuristic alerts of the host’s antivirus software. This "living-off-the-land" approach, combined with the "living-in-a-VM" strategy, creates a formidable challenge for even well-defended enterprise networks.

Campaign STAC4713: GOLD ENCOUNTER and the Payouts King Connection
Researchers at Sophos have meticulously documented two distinct campaigns involving this virtualization strategy. The first, tracked as STAC4713, was initially observed in late 2024 and has continued into the latter half of 2025. This campaign is attributed to the threat group known as GOLD ENCOUNTER, a sophisticated entity with a documented history of targeting hypervisors and VMware ESXi environments.
In the STAC4713 campaign, the attackers achieved initial access through several vectors, including vulnerabilities in exposed SonicWall VPNs and the exploitation of CVE-2025-26399, a critical flaw in the SolarWinds Web Help Desk platform. Once inside the network, the group demonstrated high levels of technical proficiency. To ensure persistence, they created a Windows scheduled task deceptively named "TPMProfiler." This task was configured to launch the QEMU emulator with SYSTEM-level privileges.
To further evade detection, the attackers disguised the virtual disk files (.qcow2) used by the VM by giving them database (.db) or dynamic link library (.dll) extensions. Inside this hidden Alpine Linux VM, the attackers loaded a formidable arsenal, including the AdaptixC2 framework, the Chisel tunneling tool, BusyBox for various utility functions, and Rclone for automated data exfiltration.
The post-infection phase of STAC4713 involved aggressive credential harvesting. The actors utilized the Volume Shadow Copy Service (VSS) via the vssuirun.exe binary to create shadow copies of the Active Directory database (NTDS.dit). They then leveraged the SMB print command to move these sensitive files, along with the SAM and SYSTEM hives, into temporary directories for analysis and subsequent exploitation.
Campaign STAC3725: Exploiting Citrix and ScreenConnect
The second campaign, identified as STAC3725, surfaced in February 2025 and showcased a different but equally effective entry method. This campaign primarily targeted NetScaler ADC and Gateway instances by exploiting the "CitrixBleed 2" vulnerability (CVE-2025-5777). This flaw allows for session hijacking and unauthorized access, providing a direct gateway into the heart of corporate infrastructures.

Upon successfully compromising a NetScaler device, the STAC3725 actors deployed a ZIP archive containing a malicious executable. This payload installed a new Windows service named "AppMgmt" and created a local administrator account under the name "CtxAppVCOMService." To maintain long-term access, the attackers installed a ScreenConnect (ConnectWise Control) client. ScreenConnect is a legitimate remote desktop tool that, when misconfigured or illicitly installed, provides attackers with a stable, high-speed connection to the victim’s environment.
Similar to the GOLD ENCOUNTER tactics, the STAC3725 campaign used ScreenConnect to drop a QEMU package. However, rather than using a pre-configured toolkit, these attackers demonstrated a more "hands-on" approach, manually compiling and installing their tools within the Alpine Linux VM. The toolkit observed in this campaign included Impacket for network protocol manipulation, KrbRelayx and Kerbrute for Kerberos attacks, BloodHound.py for Active Directory mapping, and the Metasploit Framework for general exploitation.
The Link to BlackBasta and Affiliate Evolution
Evidence gathered by Zscaler and other threat intelligence firms suggests that Payouts King is not merely a standalone operation but likely involves former affiliates of the BlackBasta ransomware collective. This connection is reinforced by the overlapping Tactics, Techniques, and Procedures (TTPs) observed across both groups.
One of the most telling similarities is the reliance on social engineering and "IT support" deception. Payouts King has been observed using "spam bombing"—flooding a user’s inbox with thousands of newsletters to distract them—followed by a fraudulent call or Microsoft Teams message from "the IT department." The attackers then trick the employee into downloading the Microsoft Quick Assist tool, giving the hackers direct control over the workstation. This method of bypassing technical controls through human manipulation has become a hallmark of the group’s initial access strategy.
Analysis of the Payouts King Encryption Scheme
Once the attackers have exfiltrated sufficient data to facilitate double extortion, they deploy the Payouts King ransomware payload. The technical architecture of the ransomware itself is designed for both speed and robustness. It employs an AES-256 (CTR mode) encryption algorithm for file data, with the unique AES keys protected by RSA-4096 public-key encryption.

To maximize the speed of the attack, especially on large file servers, the ransomware utilizes "intermittent encryption." Instead of encrypting every byte of a file, the malware encrypts specific blocks of data at intervals. This is often sufficient to render the file unusable while significantly reducing the time required to lock a large volume of data, thereby decreasing the window of time in which security teams can intervene.
The ransomware also features heavy obfuscation and anti-analysis mechanisms to hinder reverse engineering. It utilizes low-level system calls to terminate security processes and delete backups, ensuring that the victim’s recovery options are severely limited. Following the encryption process, a ransom note is dropped across the system, directing the victims to a dedicated leak site on the dark web where they are pressured to pay to prevent their data from being published.
Chronology of Observed Activity (2024–2025)
- Late 2024: Early indicators of GOLD ENCOUNTER testing QEMU-based evasion techniques in isolated environments.
- November 2025: Campaign STAC4713 is officially identified. Attackers exploit SonicWall VPNs to deploy Payouts King via Alpine Linux VMs.
- January 2025: Increased reports of Microsoft Teams-based phishing campaigns targeting enterprise employees, linked to BlackBasta-style social engineering.
- February 2025: Campaign STAC3725 begins. Exploitation of CitrixBleed 2 (CVE-2025-5777) becomes a primary entry vector for QEMU-enabled attacks.
- March 2025: SolarWinds Web Help Desk vulnerability (CVE-2025-26399) is added to the GOLD ENCOUNTER arsenal for initial access.
- April 2025: Security researchers publish comprehensive reports detailing the use of "TPMProfiler" and disguised .qcow2 files, warning the industry of the virtualization blind spot.
Broader Implications for Enterprise Security
The rise of QEMU-based ransomware delivery represents a pivotal shift in the "cat-and-mouse" game between attackers and defenders. For years, the security industry has focused on perfecting kernel-level monitoring and behavioral analysis on the host operating system. By moving the malicious logic into a virtualized guest, attackers have effectively created a sanctuary where their actions are not subject to the same scrutiny.
This development underscores the limitations of host-centric security models. When a VM is running on a host, the host OS sees the hypervisor process (qemu.exe) as a single, legitimate application. The network traffic generated by the VM often appears to originate from the host itself, making it difficult for network-based detection systems to distinguish between legitimate host traffic and malicious VM traffic without deep packet inspection and sophisticated traffic analysis.
Furthermore, the use of legitimate tools like ScreenConnect and Quick Assist highlights the ongoing challenge of "living-off-the-land." When attackers use the same tools as the IT department, the line between administrative maintenance and a security breach becomes dangerously blurred.
Defense and Mitigation Strategies
To counter these sophisticated threats, security experts recommend a multi-layered defense strategy that looks beyond traditional endpoint monitoring.
- Hypervisor Visibility: Organizations should implement monitoring solutions capable of detecting the installation and execution of unauthorized virtualization software. Monitoring for command-line arguments associated with QEMU, such as those defining network bridges or virtual disk paths, is essential.
- Scheduled Task Auditing: Regular audits of scheduled tasks, particularly those running with SYSTEM or Administrative privileges, can reveal persistence mechanisms like the "TPMProfiler" task.
- Network-Level Monitoring: Since host-based EDR may be blinded, network-based detection becomes critical. Security teams should look for unusual SSH traffic, particularly outbound connections on non-standard ports, which may indicate a reverse tunnel.
- Vulnerability Management: Rapid patching of critical edge devices, such as SonicWall VPNs and Citrix NetScaler instances, remains the most effective way to prevent the initial breach.
- Employee Awareness: Given the group’s success with social engineering via Microsoft Teams and Quick Assist, continuous security awareness training is vital to help employees recognize and report suspicious "IT support" interactions.
As ransomware groups continue to refine their methods, the industry must respond by developing more integrated security architectures that can bridge the gap between the host and the virtualized environments running upon them. The Payouts King campaigns serve as a stark reminder that in the world of cybersecurity, no tool is too legitimate to be weaponized.