Obsidian Note-Taking App Exploited in Targeted Social Engineering Campaign to Deliver PHANTOMPULSE Malware
Cybersecurity researchers have uncovered a sophisticated social engineering operation that leverages the popular note-taking application Obsidian to deploy a new breed of remote access trojan (RAT) against professionals in the financial and cryptocurrency sectors. The campaign, tracked as REF6598 by Elastic Security Labs, utilizes a multi-stage infection vector that begins on professional social networks and culminates in the execution of an AI-generated backdoor dubbed PHANTOMPULSE. By abusing the legitimate plugin ecosystem of a trusted productivity tool, the threat actors have demonstrated a high degree of creativity in bypassing traditional perimeter defenses and signature-based antivirus solutions.
The discovery highlights a growing trend where adversaries shift away from traditional software exploits, instead opting to weaponize the "human element" and the inherent trust users place in their daily workflow applications. In this instance, the attackers do not exploit a vulnerability within Obsidian itself; rather, they abuse its intended functionality—specifically its community plugin architecture—to achieve persistence and command execution on compromised Windows and macOS systems.
The Architecture of Deception: A Multi-Platform Social Engineering Strategy
The REF6598 campaign is characterized by its elaborate and patient approach to social engineering. According to technical analysis from Elastic researchers Salim Bitam, Samir Bousseaden, and Daniel Stepanic, the intrusion begins on LinkedIn. The threat actors create highly polished profiles, posing as representatives of reputable venture capital firms or investment groups. These personas are used to identify and approach high-value targets within the decentralized finance (DeFi) and cryptocurrency ecosystems.
Once initial contact is established and a rapport is built, the conversation is transitioned to Telegram. This move is a calculated tactic designed to move the victim away from the monitored environment of LinkedIn and into a more private, group-based setting. Within the Telegram group, the target is introduced to several other "partners" or "analysts" belonging to the fake venture capital firm. These additional accounts engage in simulated discussions regarding market trends, liquidity solutions, and financial strategies, providing a veneer of professional legitimacy to the operation.
The climax of this social engineering phase occurs when the attackers invite the target to collaborate on a "shared dashboard" hosted within Obsidian. Obsidian is a cross-platform Markdown-based note-taking app that allows users to create "vaults"—folders containing notes, images, and configuration files. The attackers instruct the victim to connect to a cloud-hosted vault, providing them with specific credentials and setup instructions.
The Infection Sequence: Abusing Obsidian’s Plugin Ecosystem
The core of the technical compromise lies in how Obsidian handles its community plugins. Obsidian features a robust ecosystem where third-party developers can create plugins to extend the app’s functionality. Because these plugins can execute code to modify the interface or automate tasks, Obsidian disables "Community Plugins" by default as a security measure.
To bridge this security gap, the threat actors must convince the victim to manually enable the "Installed community plugins" sync feature within their Obsidian settings. The attackers frame this as a necessary step to view the "interactive elements" of the shared dashboard. Once the victim toggles this setting, the malicious vault configuration files are synced to the local machine.

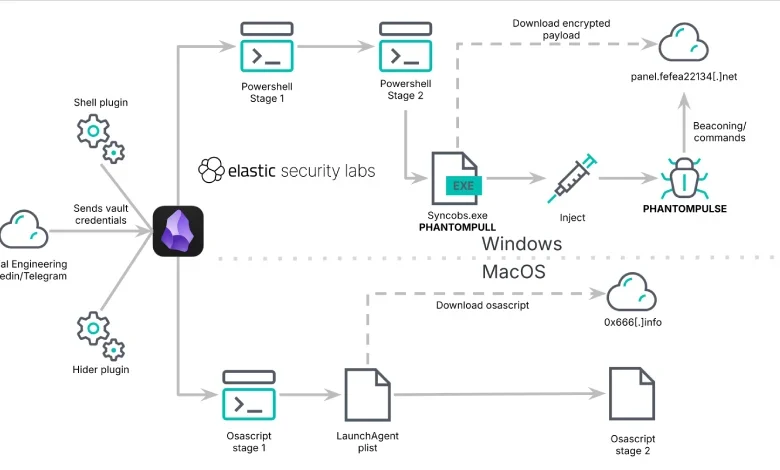
The campaign specifically weaponizes two legitimate plugins:
- Shell Commands: A plugin designed to allow users to execute terminal commands or scripts directly from Obsidian.
- Hider: A plugin used to customize the Obsidian user interface by hiding specific elements like sidebars, tooltips, or status bars.
In the REF6598 campaign, the Shell Commands plugin is configured to execute a malicious payload the moment the vault is opened. Simultaneously, the Hider plugin is used to suppress any visual indicators of the attack, such as terminal windows or status bar updates, ensuring the infection remains invisible to the user. This "living-off-the-land" (LotL) technique is particularly effective because the malicious instructions reside within JSON configuration files, which are rarely flagged by traditional antivirus software. Furthermore, because the execution is initiated by a signed and trusted Electron-based application (Obsidian), it often bypasses behavioral detection systems that focus on untrusted binaries.
PHANTOMPULSE: An AI-Generated Backdoor with Blockchain C2
The execution path diverges based on the victim’s operating system, though the ultimate goal on Windows is the deployment of the PHANTOMPULSE RAT.
The Windows Infection Path
On Windows systems, the Shell Commands plugin triggers a PowerShell script. This script acts as an initial downloader for an intermediate loader known as PHANTOMPULL. The loader is responsible for environmental checks and the decryption of the final payload, which is injected directly into the system’s memory to avoid leaving a footprint on the physical disk.
The final payload, PHANTOMPULSE, is described by researchers as an AI-generated backdoor. This suggests that the threat actors utilized Large Language Models (LLMs) to assist in writing the malware’s code, potentially to accelerate development or to create unique code structures that evade signature-based detection.
One of the most notable features of PHANTOMPULSE is its use of the Ethereum blockchain for Command-and-Control (C2) resolution. Rather than connecting to a hard-coded IP address or domain—which can be easily blocked—the malware is programmed with a specific Ethereum wallet address. It queries the blockchain to find the latest transaction associated with that wallet. The metadata or data within that transaction contains the encoded address of the actual C2 server. This "dead drop resolver" technique makes the infrastructure incredibly resilient, as the attackers can update their C2 server address simply by sending a new transaction on the public blockchain.
Once communication is established via WinHTTP, PHANTOMPULSE grants the attackers comprehensive control over the infected host. Its capabilities include:
- Collecting and exfiltrating system telemetry and hardware information.
- Capturing screenshots of the user’s desktop.
- Logging keystrokes to steal credentials and private keys.
- Uploading and downloading files.
- Executing arbitrary shell commands.
The macOS Infection Path
For users on macOS, the Shell Commands plugin delivers an obfuscated AppleScript dropper. This script attempts to contact a series of hard-coded domains to download a second-stage payload. Similar to the Windows version, the macOS dropper utilizes Telegram as a fallback dead drop resolver for C2 discovery if the primary domains are unreachable. While the exact nature of the final macOS payload remains unconfirmed because the C2 servers were offline during analysis, the intent is clearly aligned with the Windows-based espionage and data theft objectives.

Analysis of Implications and Industry Response
The REF6598 campaign represents a sophisticated evolution in the threat landscape. By targeting the financial and cryptocurrency sectors, the attackers are pursuing high-yield objectives where a single successful breach can lead to the theft of significant digital assets or sensitive market intelligence.
The use of AI-generated code in PHANTOMPULSE is a harbinger of future trends. As AI coding assistants become more prevalent, the barrier to entry for creating complex, custom malware is lowering. This allows threat actors to produce a higher volume of unique malware variants, putting additional strain on security teams that rely on traditional detection methods.
Elastic Security Labs emphasizes that the success of this campaign relies on the subversion of trust. "By abusing Obsidian’s community plugin ecosystem rather than exploiting a software vulnerability, the attackers bypass traditional security controls entirely," the researchers noted. They point out that parent-process-based detection is the critical layer of defense in these scenarios. Security tools must be configured to monitor the behavior of trusted applications like Obsidian and alert on suspicious child processes, such as the spawning of PowerShell or AppleScript in contexts that deviate from normal user activity.
Chronology of a Typical REF6598 Attack
- Reconnaissance: Attackers identify targets in the crypto/finance sector via professional networks.
- Initial Contact: A fake venture capital persona reaches out on LinkedIn with a collaboration or investment proposal.
- Platform Shift: The target is moved to a curated Telegram group to build a sense of community and trust.
- The Bait: The target is asked to review a "dashboard" or "deal flow" document within an Obsidian vault.
- The Hook: The target is guided through the process of enabling "Community Plugin Sync" in Obsidian.
- Exploitation: Upon opening the vault, the Shell Commands plugin executes the initial malicious script.
- Payload Delivery: PHANTOMPULL (Windows) or the AppleScript dropper (macOS) is fetched.
- C2 Resolution: The malware uses the Ethereum blockchain or Telegram to find the active C2 server.
- Full Compromise: PHANTOMPULSE is loaded into memory, providing the attackers with remote access and data exfiltration capabilities.
Conclusion and Defensive Recommendations
The REF6598 activity serves as a stark reminder that productivity tools, while essential for modern collaboration, also introduce new surfaces for social engineering. Organizations and individuals in high-risk sectors must remain vigilant against unsolicited professional outreach that requires the installation of specific software or the modification of application security settings.
To mitigate the risks posed by such campaigns, cybersecurity experts recommend:
- Restricting Plugin Usage: Organizations should consider blacklisting or restricting the use of plugins that allow for arbitrary code execution (like Shell Commands) in productivity apps unless there is a documented business need.
- Enhanced Endpoint Monitoring: Implementing Endpoint Detection and Response (EDR) solutions that can detect anomalous child processes originating from Electron-based applications.
- User Awareness Training: Educating employees on the risks of "social engineering to execution" pipelines, specifically regarding the dangers of enabling "sync" or "macro-like" features in unfamiliar environments.
- Blockchain Monitoring: For organizations in the crypto space, monitoring for connections to known malicious blockchain addresses or dead-drop resolution patterns can provide an early warning of infection.
While the specific campaign identified by Elastic was blocked before the attackers could finalize their objectives, the methodology remains a viable and dangerous blueprint for future operations. As software ecosystems become more interconnected and extensible, the boundary between "feature" and "vulnerability" continues to blur, requiring a more holistic and behavioral approach to digital defense.