Threat Actors Exploiting Three Windows Zero-Day Vulnerabilities Following Public Disclosure by Disgruntled Researcher
The cybersecurity landscape has been jolted by the active exploitation of three recently disclosed security vulnerabilities within the Microsoft Windows ecosystem. These flaws, which primarily target Microsoft Defender and core system components, are currently being leveraged by threat actors to achieve elevated administrative permissions or "SYSTEM" level access on compromised machines. The situation is particularly volatile because the technical details and proof-of-concept (PoC) exploit codes for these vulnerabilities were intentionally leaked to the public by a security researcher acting under the pseudonym "Chaotic Eclipse" (also known as "Nightmare-Eclipse"). This leak was reportedly a retaliatory move against the Microsoft Security Response Center (MSRC), following a breakdown in the communication and disclosure process regarding these specific bugs.
Since the beginning of April 2026, the cybersecurity community has watched as these vulnerabilities transitioned from theoretical risks to active threats. Of the three flaws identified, two are classified as Local Privilege Escalation (LPE) vulnerabilities within Microsoft Defender, while the third allows an attacker to manipulate the antivirus software’s update mechanism. Despite Microsoft’s efforts to remediate the situation during its most recent patch cycle, two of the three vulnerabilities remain unpatched, leaving millions of Windows systems vulnerable to exploitation.
The Anatomy of the Exploits: BlueHammer, RedSun, and UnDefend
The three vulnerabilities—dubbed BlueHammer, RedSun, and UnDefend by the researcher—represent a significant risk to the integrity of Windows-based environments. Each serves a specific purpose in the attack chain, allowing threat actors to move from initial access to full system control.
BlueHammer, now tracked as CVE-2026-33825, is a Local Privilege Escalation flaw in Microsoft Defender. It allows a low-privileged user to gain SYSTEM-level permissions, the highest level of authority on a Windows operating system. While Microsoft addressed this specific issue in the April 2026 Patch Tuesday updates, the period between the PoC leak and the patch release saw a surge in exploitation attempts.
The second vulnerability, RedSun, remains perhaps the most dangerous of the trio. Also an LPE flaw targeting Microsoft Defender, RedSun exploits a logic error in how the antivirus engine handles malicious files tagged for cloud analysis. According to the researcher, when Windows Defender identifies a file with a specific "cloud tag," the system attempts to rewrite the file back to its original location. By abusing this behavior, an attacker can trick the system into overwriting critical system files with malicious code, effectively granting the attacker administrative privileges. RedSun remains unpatched and affects a wide range of operating systems, including Windows 10, Windows 11, and Windows Server 2019 and later.

The third component, UnDefend, is a utility exploit that allows a standard user to block Microsoft Defender from receiving definition updates. By preventing the antivirus from updating its signature database, attackers can ensure that newer malware variants remain undetected on the system for longer periods, providing a window of opportunity for data exfiltration or the deployment of ransomware.
Chronology of the Disclosure and Exploitation
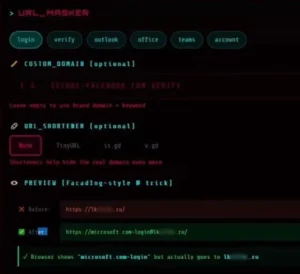
The timeline of these events highlights a rapid escalation from disclosure to active threat. The researcher, "Chaotic Eclipse," began publishing the exploit codes in early April 2026. The motivation cited was a perceived lack of urgency or professional courtesy from Microsoft’s security team during the initial private reporting phase. By releasing the PoCs to GitHub, the researcher bypassed the traditional "Coordinated Vulnerability Disclosure" (CVD) model, which typically gives vendors 90 days to develop a patch before the details are made public.
On April 10, 2026, security researchers at Huntress Labs began observing the first signs of BlueHammer being used in real-world attacks. These early incidents appeared to be opportunistic, targeting organizations that had not yet prepared for the sudden availability of the exploit.
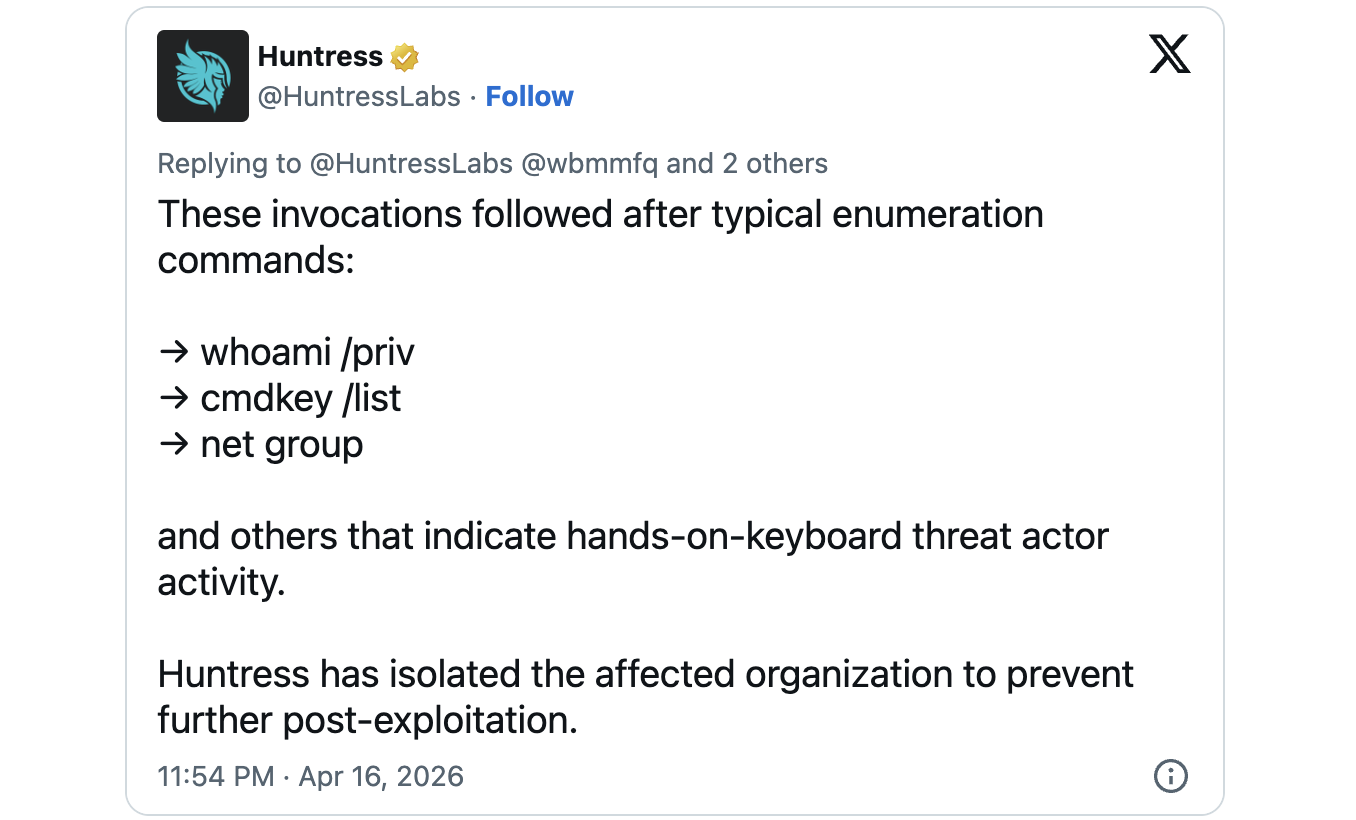
By mid-April, following the release of the April Patch Tuesday updates, the focus shifted to RedSun and UnDefend. On Thursday, Huntress Labs confirmed that "hands-on-keyboard" threat actors were actively using these two unpatched exploits. In one documented case, a Windows device was breached via a compromised SSLVPN user account. Once inside the network, the attackers deployed the RedSun and UnDefend exploits to escalate their privileges and disable security updates, signaling a sophisticated and targeted approach rather than automated malware.
Evidence of In-the-Wild Attacks
The findings from Huntress Labs provide a sobering look at how quickly threat actors can weaponize public research. The "hands-on-keyboard" designation is particularly concerning to security analysts. Unlike automated worms or viruses, hands-on-keyboard activity indicates that a human attacker is actively navigating the network, choosing targets, and adapting their tactics in real-time.
"The Huntress SOC is observing the use of Nightmare-Eclipse’s BlueHammer, RedSun, and UnDefend exploitation techniques," the firm stated in a public advisory. Their telemetry suggests that the attackers are not just testing the PoCs but are integrating them into their standard operating procedures for post-compromise activity. The use of a compromised SSLVPN for initial access underscores the importance of perimeter security; however, the subsequent use of the zero-day exploits shows that even with strong perimeter defenses, internal system vulnerabilities can lead to a total compromise.

The Conflict Between Independent Researchers and Microsoft
This incident has reignited the long-standing debate over the relationship between independent security researchers and large technology corporations. The "disgruntled researcher" phenomenon is not new, but the scale of the impact in this case is significant.
Microsoft, for its part, maintains a formal stance on vulnerability disclosure. A spokesperson for the company emphasized their commitment to investigating reported issues and protecting customers. "We support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure," the company stated.
However, researchers often argue that the CVD process can be opaque, with some bugs being dismissed as "won’t fix" or "by design," only to be exploited later. Chaotic Eclipse’s decision to leak the exploits was a "protest" against this process, but it has left the broader user base caught in the crossfire between the researcher’s ethics and the vendor’s response time.
Technical Implications of Privilege Escalation
To understand the severity of these vulnerabilities, one must consider the role of Local Privilege Escalation in a modern cyberattack. Most initial entry points—such as phishing or exploited VPN credentials—grant an attacker the permissions of a standard user. In a well-secured environment, a standard user has limited access to sensitive data and cannot install software or modify system settings.
LPE vulnerabilities like BlueHammer and RedSun are the "skeleton keys" of the digital world. They allow an attacker to bypass these restrictions. Once an attacker gains SYSTEM privileges, they effectively "own" the machine. They can disable security software, install persistent backdoors, dump credentials from memory (such as those of a Domain Administrator), and move laterally through the network to infect other machines. The irony that these specific vulnerabilities exist within Microsoft Defender—the very tool meant to prevent such actions—is not lost on the security community.
Broader Impact and Defensive Recommendations
The existence of unpatched zero-day exploits in a core security product like Microsoft Defender creates a complex challenge for IT administrators. Because RedSun and UnDefend remain unpatched, standard update procedures are currently insufficient to mitigate the risk.
Security experts recommend several layers of defense to counter these threats:
- Enhanced Monitoring: Organizations should increase their focus on monitoring for unusual activity related to Microsoft Defender processes. Specifically, any unauthorized attempts to modify system files or block update services should be treated as high-priority alerts.
- Perimeter Hardening: Since the exploits require an initial foothold, securing entry points like SSLVPNs with multi-factor authentication (MFA) and up-to-date patching is critical.
- Endpoint Detection and Response (EDR): While Microsoft Defender is a robust tool, having a secondary EDR solution or advanced logging (such as Sysmon) can provide the visibility needed to catch an attacker using an LPE exploit.
- Principle of Least Privilege: Limiting the number of users with any form of administrative access can slow down an attacker, though LPE exploits are specifically designed to circumvent these limits.
The Future of Coordinated Vulnerability Disclosure
As the industry moves forward, the fallout from the BlueHammer, RedSun, and UnDefend leaks will likely prompt a re-evaluation of how vendors and researchers interact. While Microsoft has addressed one of the three flaws, the remaining two continue to pose a threat to global digital infrastructure.
The incident serves as a reminder that the window between the disclosure of a vulnerability and its exploitation is shrinking. In this case, the window was non-existent, as the exploits were released alongside the disclosure. For organizations, the lesson is clear: security cannot rely solely on patches. A proactive, multi-layered defense strategy that assumes a breach will eventually occur is the only way to remain resilient in an era where zero-day exploits are increasingly accessible to the masses.
As of the latest reports, Microsoft has not provided a specific timeline for when the RedSun and UnDefend vulnerabilities will be officially patched. Until then, the cybersecurity community remains on high alert, monitoring for the next wave of attacks using these "Nightmare-Eclipse" techniques.