Cyber Security Landscape Shift as Creative Exploits and Legacy Vulnerabilities Challenge Global Infrastructure
The global cybersecurity landscape has reached a critical juncture where the convergence of sophisticated new methodologies and the persistence of legacy vulnerabilities has created a multifaceted threat environment for enterprises and government agencies alike. Recent intelligence reports indicate a significant uptick in "creative" exploitation techniques, where threat actors are moving away from traditional malware in favor of more nuanced, social-engineering-heavy, and "living off the land" strategies. Simultaneously, the industry continues to grapple with the resurgence of ancient vulnerabilities—flaws discovered years or even decades ago that remain unpatched in critical systems. This dual-threat environment is further complicated by a volatile software supply chain, where the dependencies of modern applications have become the primary vector for large-scale intrusions.
The Evolution of Creative Exploitation and Social Engineering
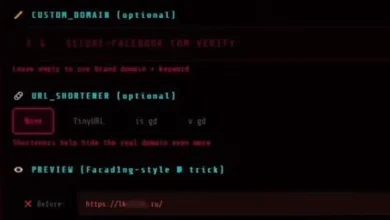
In recent months, cybersecurity researchers have documented a shift in how threat actors gain initial access to secure networks. Rather than relying solely on brute-force attacks or known exploits, attackers are increasingly utilizing creative psychological manipulation and AI-driven deepfakes to bypass sophisticated security perimeters. One notable trend involves "MFA Fatigue" attacks, where attackers bombard a target with multi-factor authentication requests until the exhausted user inadvertently approves the login. This method exploits human psychology rather than software code, making it significantly harder for traditional automated systems to detect.
Furthermore, the rise of generative artificial intelligence has empowered lower-level cybercriminals to produce highly convincing phishing campaigns in multiple languages, devoid of the grammatical errors that once served as red flags for security-conscious users. By automating the reconnaissance phase, attackers can now tailor their "creative" lures to the specific professional roles of their targets, increasing the success rate of initial penetrations. This evolution suggests that the human element remains the weakest link in the security chain, despite the billions of dollars invested in technical safeguards.
The Persistence of Legacy Vulnerabilities
While the industry often focuses on "Zero-Day" exploits—vulnerabilities unknown to the software vendor—the reality of the current threat landscape is that "N-Day" exploits remain the most common cause of breaches. These are vulnerabilities for which patches have existed for years, yet remain unapplied across a vast array of global infrastructure. Security audits conducted in the first half of the year revealed that a staggering percentage of enterprise environments still harbor vulnerabilities from as far back as 2010.
The reasons for this persistence are rooted in the concept of "technical debt." Many organizations operate mission-critical systems on legacy hardware or software that cannot be updated without risking significant downtime or system failure. In sectors such as manufacturing and healthcare, where uptime is a matter of physical safety, the risk of a patch breaking a system is often perceived as greater than the risk of a potential cyberattack. Consequently, threat actors continue to find success using exploit kits that are over a decade old, targeting the low-hanging fruit of unpatched industrial control systems and aging enterprise resource planning (ERP) software.
Supply Chain Volatility and Dependency Risks
The modern software development lifecycle relies heavily on open-source libraries and third-party dependencies. This interconnectedness has birthed a "supply chain drama" that has become a recurring theme in major security incidents. By compromising a single widely-used library, an attacker can gain access to thousands of downstream organizations simultaneously. This "one-to-many" attack vector was most famously demonstrated in the SolarWinds and MOVEit incidents, but recent data suggests the problem is worsening.
Analysis of public repositories such as PyPI (Python Package Index) and NPM (Node Package Manager) has shown a surge in "typosquatting" and "dependency confusion" attacks. In these scenarios, hackers upload malicious packages with names nearly identical to popular legitimate ones. When developers or automated build systems accidentally pull the malicious code, the backdoor is integrated directly into the organization’s proprietary software. This shift toward targeting the developer environment marks a strategic move by threat actors to bypass the hardened production environment entirely.
Chronology of Recent Cyber Developments
To understand the current state of digital security, it is necessary to examine the timeline of events that have shaped the recent weeks:
- Phase 1: Identification of New Vector (T-Minus 30 Days): Researchers identified a new strain of malware that resides entirely in the system’s volatile memory (RAM), leaving no trace on the physical hard drive. This "fileless" approach allows attackers to evade traditional antivirus software.
- Phase 2: Supply Chain Injection (T-Minus 20 Days): A popular open-source utility used for data visualization was found to have been compromised at the source. The malicious update remained undetected for 72 hours, during which it was downloaded by approximately 5,000 organizations.
- Phase 3: Exploitation of Legacy Flaws (T-Minus 10 Days): A coordinated ransomware campaign targeted regional government offices using a 2017 vulnerability in the Server Message Block (SMB) protocol. The attack highlighted the lack of patching in public sector infrastructure.
- Phase 4: Exposure and Takedown (T-Minus 2 Days): A joint operation between international law enforcement agencies and private security firms successfully dismantled the infrastructure of a major Ransomware-as-a-Service (RaaS) provider. The operation resulted in the seizure of servers and the release of decryption keys for past victims.
Supporting Data and Industry Statistics
The scale of the current threat is reflected in recent industry metrics. According to data compiled from global security operations centers (SOCs):
- Mean Time to Patch (MTTP): The average time for an enterprise to apply a critical patch remains at 65 days, while threat actors typically begin exploiting a newly disclosed vulnerability within 15 days.
- Ransomware Demands: The average ransom demand has seen a 20% increase year-over-year, driven by "big game hunting" tactics where attackers target high-revenue corporations.
- Credential Theft: Over 60% of all data breaches now involve the use of stolen or compromised credentials, emphasizing the decline of the traditional password as a viable security measure.
- Mobile Store Security: Despite rigorous vetting processes, official app stores removed over 1,500 applications in the last quarter that were found to contain hidden "dropper" code designed to download secondary malicious payloads after installation.
Official Responses and Regulatory Analysis
Governments and regulatory bodies have responded to these escalating threats with increased pressure on both software vendors and end-users. The Cybersecurity and Infrastructure Security Agency (CISA) in the United States has expanded its "Known Exploited Vulnerabilities" (KEV) catalog, mandating that federal agencies patch specific flaws within strict timeframes. This move is designed to set a standard for the private sector, encouraging a more proactive approach to vulnerability management.
In Europe, the implementation of the NIS2 Directive is forcing organizations in critical sectors to adopt more stringent cybersecurity risk management measures and reporting obligations. The consensus among policymakers is that "voluntary" security measures have failed to protect national infrastructure, and that mandatory standards are necessary to ensure a baseline level of resilience.
Industry experts and CTOs have reacted with a mixture of caution and calls for a "back-to-basics" approach. Statements from leading security firms suggest that while advanced threat hunting and AI-driven defense are valuable, they cannot replace fundamental hygiene. "We are seeing a trend where organizations are buying the most expensive ‘AI-powered’ security tools while failing to implement basic network segmentation or regular patching," noted one senior analyst during a recent industry summit. "The basics still matter more than most people want to admit."
Broader Impact and Future Implications
The long-term implications of these trends point toward a future where "cyber resilience" is prioritized over "cyber security." The assumption is no longer that an organization can prevent all attacks, but rather how quickly it can detect, contain, and recover from an inevitable breach. This shift in mindset is driving investment in immutable backups, automated incident response, and zero-trust architecture.
The "creative" nature of modern threats means that the boundary between digital and physical security is blurring. As hackers target supply chains and legacy industrial systems, the potential for real-world disruption—ranging from power outages to healthcare delays—becomes a tangible risk. The exposure of threat actors with "receipts" (forensic evidence of their activities) provides a temporary reprieve, but the decentralized nature of cybercrime ensures that new actors will quickly fill the vacuum.
In conclusion, the current "Threatsday" summary serves as a stark reminder that the digital frontier remains a high-risk environment. The combination of creative social engineering, the long tail of legacy vulnerabilities, and the inherent risks of the software supply chain requires a holistic and disciplined approach to defense. For organizations and individuals alike, the message is clear: check your patches, scrutinize your dependencies, and maintain a healthy skepticism toward even the most official-looking digital platforms. Staying sharp and maintaining rigorous logs are not merely technical requirements but essential components of modern operational survival. The internet will undoubtedly cook up fresh chaos in the coming weeks; the only variable is the readiness of those it targets.