legacy
-
Cybersecurity
Cyber Security Landscape Shift as Creative Exploits and Legacy Vulnerabilities Challenge Global Infrastructure
The global cybersecurity landscape has reached a critical juncture where the convergence of sophisticated new methodologies and the persistence of…
Read More » -
Web Development
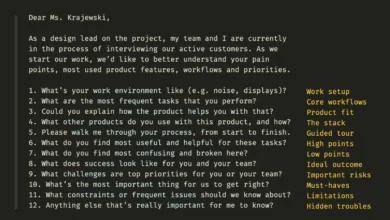
Revitalizing the Digital Dinosaur: Strategies for Enhancing User Experience in Legacy Systems
The persistent challenge of modernizing outdated digital infrastructure, often referred to as "legacy systems," is a critical hurdle for organizations…
Read More » -
Cybersecurity
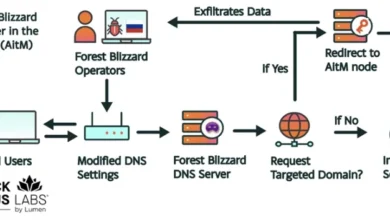
Russian Intelligence Exploits Thousands of Legacy Routers to Siphon Microsoft User Data in Global Espionage Campaign
Cybersecurity researchers and government agencies have issued a high-level alert regarding a sophisticated yet structurally simple espionage campaign orchestrated by…
Read More »