Hacking
-
Cybersecurity

The Evolution of Underground Credit Card Marketplaces and the Rise of Professionalized Fraud Vetting Standards
The underground market for stolen credit card data has entered a new era of professionalization, shifting away from opportunistic, chaotic…
Read More » -
Cybersecurity

NIST Implements Risk-Based Prioritization for National Vulnerability Database Enrichment Amid Record CVE Growth
The National Institute of Standards and Technology (NIST) has officially transitioned to a risk-based prioritization model for the National Vulnerability…
Read More » -
Cybersecurity

Over Eighty Thousand Hikvision Surveillance Cameras Remain Vulnerable to Critical Command Injection Flaw Nearly One Year After Patch Release
A significant security gap in global surveillance infrastructure has been identified as more than 80,000 Hikvision cameras remain unpatched against…
Read More » -
Cybersecurity
Global Law Enforcement Coalition Dismantles Massive IoT Botnet Infrastructure Responsible for Record-Breaking DDoS Attacks
In a significant blow to the global cybercrime ecosystem, the United States Department of Justice (DOJ), in coordination with international…
Read More » -
Cybersecurity

Grinex Crypto Exchange Suspends Operations Following 13.7 Million Dollar Hack and Allegations of Western Intelligence Involvement
The Kyrgyzstan-based cryptocurrency exchange Grinex has officially suspended all trading and withdrawal operations following a sophisticated cyberattack that resulted in…
Read More » -
Cybersecurity

Google Bolsters Android Privacy and Ad Safety with New Play Policies and Gemini AI Integration
Google has unveiled a comprehensive suite of updates to its Play Store policies and advertising ecosystem, signaling a significant shift…
Read More » -
Cybersecurity

Lockbit 3.0 and Conti Offshoots Drive Massive Resurgence in Global Ransomware Attacks
The global cybersecurity landscape witnessed a significant escalation in ransomware activity throughout July 2022, marking a definitive end to the…
Read More » -
Cybersecurity
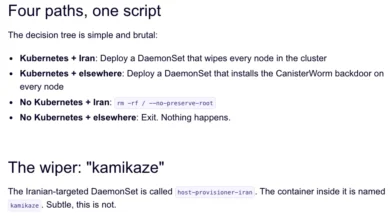
TeamPCP Weaponizes Cloud Infrastructure and Supply Chain Vulnerabilities to Deploy Data-Wiping Malware Targeting Iranian Systems
The landscape of global cyber warfare has witnessed a significant escalation as a financially motivated threat actor known as TeamPCP…
Read More » -
Cybersecurity

Payouts King Ransomware Leverages QEMU Virtual Machines to Evade Endpoint Detection and Establish Stealthy Network Backdoors
The cybersecurity landscape is witnessing a sophisticated evolution in ransomware delivery mechanisms, as threat actors increasingly turn to legitimate virtualization…
Read More » -
Cybersecurity

Microsoft Defender Security Flaws Under Active Exploitation Following Zero-Day Disclosure by Independent Researcher
Cybersecurity researchers have issued an urgent warning regarding the active exploitation of three recently identified vulnerabilities within Microsoft Defender, the…
Read More »
