Massive Cyberattack Linked to Iran-Backed Hacktivists Hits Global Medical Technology Giant Stryker
Stryker Corporation, a cornerstone of the global medical technology sector, is currently grappling with a catastrophic cyberattack that has paralyzed its international operations and raised urgent concerns regarding the stability of the healthcare supply chain. The attack, characterized as a massive data-wiping operation, has been claimed by Handala, a hacktivist collective with documented ties to the Iranian government’s intelligence apparatus. As the company struggles to restore its systems, reports indicate that tens of thousands of devices have been rendered useless, forcing a total cessation of work at major hubs and disrupting critical medical services across multiple continents.
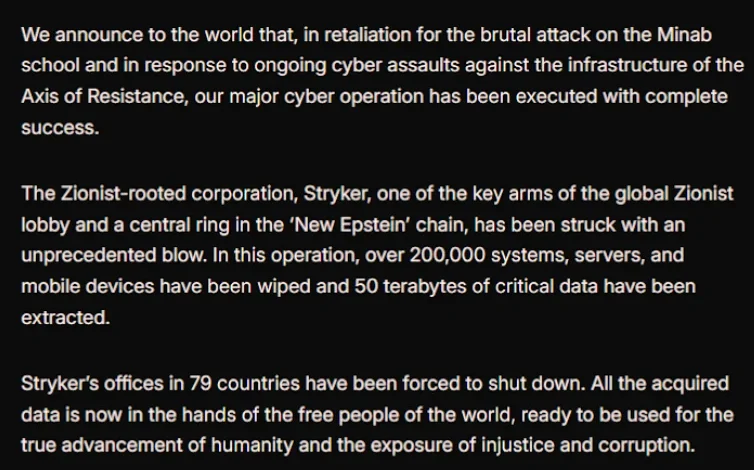
Based in Kalamazoo, Michigan, Stryker is a Fortune 500 company and a dominant force in the medical equipment industry, reporting over $25 billion in global sales in the previous fiscal year. With a workforce of approximately 56,000 employees operating across 61 countries, the company’s influence spans orthopedic implants, surgical equipment, and neurotechnology. The scale of the current disruption is unprecedented for a firm of its size, with the Handala group claiming to have successfully erased data from more than 200,000 systems, including servers, workstations, and mobile devices, effectively "turning off" the company’s digital presence in 79 countries.
The Genesis of the Attack and Geopolitical Context
The cyber assault on Stryker appears to be a direct act of digital retaliation tied to escalating geopolitical tensions between the United States and Iran. In a lengthy manifesto disseminated via the Telegram messaging app, Handala stated that the wiper attack was a response to a February 28 missile strike that targeted an Iranian educational facility. According to reports from The New York Times, an internal military investigation recently concluded that the United States was responsible for the Tomahawk missile strike, which resulted in the deaths of at least 175 individuals, the majority of whom were children.
Handala’s messaging framed the attack on Stryker not merely as a criminal enterprise, but as a "liberation" of data. The group’s statement asserted that the acquired data is now "in the hands of the free people of the world" and will be used to "expose injustice and corruption." Furthermore, the group labeled Stryker a "Zionist-rooted corporation," a designation likely stemming from Stryker’s 2019 acquisition of OrthoSpace, an Israeli-based medical technology firm. This narrative aligns with the group’s historical pattern of targeting entities with perceived links to the United States or Israel.
Cybersecurity researchers at Palo Alto Networks’ Unit 42 have closely monitored Handala since its emergence in late 2023. Their analysis identifies Handala as a sophisticated persona maintained by "Void Manticore," a threat actor affiliated with Iran’s Ministry of Intelligence and Security (MOIS). While many hacktivist groups engage in low-level distributed denial-of-service (DDoS) attacks, Handala is known for "quick and dirty" destructive operations that leverage supply-chain footholds to maximize damage and psychological impact.
Technical Execution: The Weaponization of Microsoft Intune
While typical cyberattacks involve ransomware designed to encrypt data for profit, the strike against Stryker utilized "wiper" tactics intended for pure destruction. However, the methodology used in this instance appears particularly sophisticated. According to technical sources familiar with the incident, the perpetrators did not rely solely on traditional malware payloads. Instead, they appear to have gained unauthorized access to Stryker’s Microsoft Intune environment.
Microsoft Intune is a cloud-based endpoint management solution used by large enterprises to manage security policies and software deployment across thousands of devices. It includes a "remote wipe" feature designed to protect sensitive data if a laptop or mobile phone is lost or stolen. By compromising the administrative console of this service, the attackers were able to issue a legitimate "wipe" command to every connected device in the Stryker network. This approach allowed the attackers to bypass many traditional antivirus defenses, as the command to erase the data came from a trusted internal management system.
The results were immediate and devastating. In Ireland, home to Stryker’s largest manufacturing and research hub outside the United States, more than 5,000 employees were sent home as their laptops and workstations spontaneously reset to factory settings. Reports from the Irish Examiner noted that employees lost access to all professional tools, including Microsoft Outlook and internal databases. In the United States, visitors to the company’s headquarters were greeted by a recorded message citing a "building emergency," while internal communications shifted to personal platforms like WhatsApp as the corporate network collapsed.
A Timeline of the Escalation
The crisis at Stryker did not occur in a vacuum but followed a specific sequence of events that highlights the intersection of physical warfare and cyber retaliation:
- February 28, 2026: A Tomahawk missile strike hits a school in Iran, causing mass casualties.
- Early March 2026: Investigations by international media and military analysts begin to point toward U.S. involvement in the strike.
- March 11, 2026 (Morning): Handala issues its manifesto on Telegram, claiming the destruction of Stryker’s global network.
- March 11, 2026 (Mid-day): Stryker hubs in Ireland and the U.S. report total system failures. Employees are evacuated or sent home.
- March 11, 2026 (Afternoon): Reports emerge from U.S. hospitals regarding an inability to place orders for surgical supplies.
- March 12, 2026: State emergency medical services (EMS) in the U.S. confirm that Stryker’s online clinical services, including LIFENET, have been disabled as a precaution or due to the attack.
Immediate Impact on the Healthcare Supply Chain
The ramifications of the Stryker outage extend far beyond the company’s balance sheet, posing a direct threat to patient care in hospitals worldwide. Stryker is a primary supplier of the "bread and butter" tools of modern surgery, ranging from orthopedic power tools and joint replacements to surgical sponges and advanced imaging systems.
A healthcare professional at a major U.S. university medical system, speaking on the condition of anonymity, described the situation as a "real-world supply chain crisis." Because many hospitals operate on a "just-in-time" inventory model, the inability to communicate with Stryker’s ordering systems means that scheduled surgeries could be delayed or canceled within days if the outage persists. "Pretty much every hospital in the U.S. that performs surgeries uses their supplies," the expert noted.
Furthermore, the attack has disrupted critical clinical workflows. In Maryland, the Institute for Emergency Medical Services Systems issued a memo stating that Stryker’s LIFENET system—a cloud-based platform that allows paramedics to transmit EKG data from ambulances to emergency rooms—was impacted. This system is vital for treating ST-elevation myocardial infarction (STEMI) patients, as it allows doctors to prepare for a heart attack patient’s arrival before they even reach the hospital doors. Without LIFENET, paramedics must rely on verbal radio consultations, a slower process that can lead to life-threatening delays in cardiac care.
Official Responses and Industry Vigilance
Despite the severity of the reports, official statements have remained cautious. John Riggi, the National Advisor for Cybersecurity and Risk for the American Hospital Association (AHA), stated that the organization is actively monitoring the situation. "We are aware of reports of the cyberattack against Stryker and are actively exchanging information with the hospital field and the federal government," Riggi said. He added that while direct operational disruptions to hospitals were not yet widespread, the situation could change rapidly as hospitals evaluate their reliance on Stryker’s technology and supplies.
Stryker has yet to release a detailed public recovery plan, and its primary communication channels remain largely offline. The company’s internal focus appears to be on containing the "remote wipe" command and preventing further data loss. On social media platforms like Reddit, individuals identifying as Stryker IT staff have urged colleagues to disconnect devices from the internet and uninstall Intune management profiles immediately to save remaining data.
Analysis: The Shift to Destructive "Hacktivism"
The attack on Stryker represents a significant shift in the threat landscape for the healthcare and medical technology sectors. For years, the primary concern was ransomware—where data is held hostage for money. However, the rise of state-affiliated "hacktivist" groups like Handala signals a transition toward purely destructive motives.
When a nation-state actor uses a "wiper" against a critical infrastructure provider, the goal is not financial gain but the erosion of public trust and the disruption of societal functions. By targeting a company like Stryker, which sits at the heart of the medical supply chain, the attackers have found a way to project power and inflict pain on a global scale without firing a single shot.
This incident also serves as a stark warning regarding the security of centralized management tools like Microsoft Intune. While these services provide immense efficiency for IT departments, they also create a "single point of failure." If an attacker gains the "keys to the kingdom" of an endpoint management system, they no longer need to infect individual computers with viruses; they can simply tell the system to delete itself.
As Stryker begins the arduous process of rebuilding its digital infrastructure from the ground up, the global healthcare community is left to reckon with its vulnerabilities. The reliance on a handful of massive suppliers for critical medical needs ensures that a digital strike against one company can have a ripple effect that reaches the operating rooms of thousands of hospitals, turning a geopolitical dispute into a matter of life and death for patients thousands of miles away.