Building Resilient Foundations with Azure IaaS Strategies for Navigating Infrastructure Disruption and Enhancing Enterprise Continuity

The modern enterprise landscape is defined by an uncompromising demand for 24/7 availability, where even minutes of downtime can translate into millions of dollars in lost revenue and irreversible damage to brand reputation. As organizations increasingly migrate mission-critical workloads to the cloud, Microsoft has intensified its focus on the foundational pillars of Infrastructure as a Service (IaaS), releasing new guidance and capabilities designed to transform resiliency from an operational afterthought into a core architectural principle. This initiative, part of an ongoing series dedicated to Azure IaaS best practices, highlights a fundamental shift in the industry: the transition from attempting to prevent all disruptions to designing systems that can absorb, isolate, and recover from them with minimal impact.
The Paradigm Shift: Designing for Inevitable Disruption
In the early iterations of cloud computing, many organizations treated disruption as an "edge case"—a rare occurrence that could be managed through basic backups. However, the complexity of modern distributed systems has rendered this approach obsolete. Hardware failures, routine maintenance cycles, localized power outages, and regional environmental events are no longer "if" scenarios but "when" scenarios. Microsoft’s latest framework for Azure IaaS emphasizes that a resilient infrastructure is one that assumes disruption will occur.
The goal is not to achieve a theoretical 100% uptime through the elimination of all risks, which is statistically impossible, but to ensure that services remain available and recovery happens with high predictability. This requires a "shared responsibility" model. While Microsoft provides a resilient platform foundation through its global data center footprint and built-in service features, the ultimate outcome depends on how customers configure their specific environments. This includes the strategic placement of compute resources, the selection of data redundancy models, and the implementation of intelligent traffic routing.
The Economic Context of Infrastructure Resilience
The drive toward enhanced IaaS resiliency is fueled by the escalating costs of downtime. According to industry benchmarks from Gartner, the average cost of IT downtime is approximately $5,600 per minute, though for high-volume e-commerce or financial services firms, this figure can exceed $540,000 per hour. Beyond the immediate financial loss, organizations face regulatory scrutiny and the potential loss of customer trust, which is often harder to recover than data.
In this context, Azure IaaS provides a centralized suite of tools via the Azure IaaS Resource Center, offering a roadmap for organizations to move beyond "lift and shift" migrations. The objective is to modernize the infrastructure layer during the transition to the cloud, ensuring that legacy vulnerabilities are not simply replicated in a virtualized environment.
Compute Resiliency: Isolation and Scale
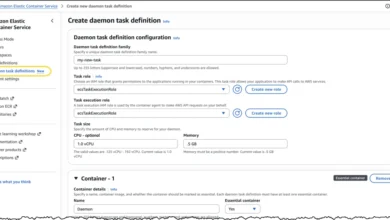
At the heart of the resilient infrastructure are compute resources, which must be protected against both localized hardware failures and broader data center outages. Microsoft identifies two primary mechanisms for achieving this: Virtual Machine Scale Sets and Availability Zones.
Virtual Machine Scale Sets allow for the automated deployment and management of a group of load-balanced VMs. By distributing these instances across "fault domains" (groups of hardware that share a common power source and network switch) and "update domains" (groups of VMs that can be rebooted simultaneously during maintenance), Azure ensures that a single point of hardware failure does not take down an entire application tier.
For higher-level protection, Azure Availability Zones provide physical separation within a single Azure region. Each zone consists of one or more data centers equipped with independent power, cooling, and networking. By architecting applications to run across multiple zones, organizations can maintain continuity even if an entire data center experiences a catastrophic event. This level of isolation is critical for front-end and application tiers that must remain responsive to user requests regardless of underlying infrastructure stress.
Storage Redundancy: Protecting the Data Lifecycle
While compute resiliency keeps applications running, storage resiliency ensures that the data driving those applications remains durable and accessible. Azure offers a hierarchy of redundancy models tailored to different risk profiles:
- Locally Redundant Storage (LRS): Replicates data three times within a single data center. This protects against disk or rack failure but not against data center-wide incidents.
- Zone-Redundant Storage (ZRS): Replicated across three availability zones within a region. This is often the recommended "sweet spot" for high availability, providing protection against zonal outages without the latency associated with cross-region replication.
- Geo-Redundant Storage (GRS) and Read-Access Geo-Redundant Storage (RA-GRS): These models extend protection to a secondary geographic region hundreds of miles away. In the event of a regional disaster, data remains safe and, in the case of RA-GRS, readable from the secondary site.
The choice of storage model directly impacts an organization’s Recovery Point Objective (RPO)—the maximum amount of data loss that is acceptable—and Recovery Time Objective (RTO)—the duration of time within which a service must be restored. For stateful applications, where data integrity is paramount, these storage decisions are the bedrock of the disaster recovery strategy.
Networking: The Invisible Link to Continuity
A common pitfall in resiliency planning is focusing exclusively on servers and databases while neglecting the network. A workload is effectively offline if users cannot reach it, even if the backend is healthy. Azure’s networking stack—including Azure Load Balancer, Application Gateway, Traffic Manager, and Azure Front Door—acts as the "traffic controller" for the cloud.
Azure Load Balancer operates at Layer 4 (TCP/UDP), distributing incoming traffic among healthy service instances. For web applications, Application Gateway provides Layer 7 routing, offering features like Web Application Firewall (WAF) integration and cookie-based affinity. On a global scale, Azure Front Door and Traffic Manager allow for seamless failover between regions. If a primary region becomes unresponsive, these services automatically redirect traffic to the nearest healthy endpoint, often making the disruption invisible to the end user.
Case Study: Carne Group’s Transition to Resilient Infrastructure
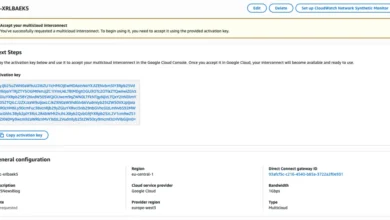
The practical application of these principles is visible in the recent migration efforts of Carne Group, a leading provider of fund management solutions. Facing the need to modernize their operations, Carne Group utilized Azure Site Recovery in conjunction with Infrastructure as Code (IaC) via Terraform.
Stéphane Bebrone, Global Technology Lead at Carne Group, noted that the move to Azure was not merely a change in hosting but a transformation of their recovery capabilities. "With IaC in place, we could easily build a duplicate site in another region," Bebrone stated. "Even in the event of a worst-case scenario, we could be back up and running more or less in the same day."
By using Terraform to define their "landing zones," Carne Group eliminated the risk of configuration drift—a common issue where manual changes to infrastructure over time lead to inconsistencies that can cause recovery efforts to fail. This automated approach ensures that the recovery environment is a perfect mirror of the production environment, providing high confidence in the organization’s failover procedures.
The Role of Automation and Future Developments
Microsoft is also addressing the "maintenance" phase of resiliency. At the recent Ignite conference, the company introduced "Resiliency in Azure" in preview. This tool is designed to help organizations assess their current deployment against best practices, identify single points of failure, and simulate faults to validate recovery paths. A public preview is slated for Microsoft Build 2026, signaling a long-term commitment to providing proactive resiliency auditing tools.
Furthermore, services like Azure Site Recovery (ASR) have become foundational for regional resilience. ASR allows for the continuous replication of VMs from a primary region to a secondary one. Crucially, it gives IT administrators control over the "orchestration" of recovery, allowing them to define the order in which VMs are powered on to respect application dependencies.
Analysis of Implications: The Competitive Edge of Uptime
The shift toward deep-stack resiliency in IaaS represents a maturing of the cloud market. In the previous decade, the primary motivator for cloud adoption was cost savings or agility. In the current decade, the motivator is increasingly "resiliency as a competitive advantage." Organizations that can demonstrate superior uptime and faster recovery are better positioned to win enterprise contracts and maintain consumer loyalty.
However, this complexity introduces a new challenge: the skills gap. Designing for multi-zone and multi-region resiliency requires a high level of expertise in cloud-native architecture. Microsoft’s push to provide more "built-in" capabilities and automated guidance is a direct response to this challenge, attempting to lower the barrier to entry for high-availability design.
Chronology of Azure Resiliency Evolution
- Phase 1 (Legacy): Focus on basic VM availability and manual backups.
- Phase 2 (Regional Expansion): Introduction of Availability Sets to protect against hardware rack failures.
- Phase 3 (Zonal Maturity): Launch of Availability Zones, providing 99.99% SLAs for VMs across multiple zones.
- Phase 4 (Global Orchestration): Integration of Azure Front Door and Site Recovery to manage cross-region failovers.
- Phase 5 (The Current Era): Emphasis on "Resiliency by Design" using IaC, automated assessment tools like "Resiliency in Azure," and AI-driven traffic management to predict and circumvent disruptions before they impact the user.
As Azure IaaS continues to evolve, the integration of compute, storage, and networking into a unified resiliency strategy will remain the hallmark of a sophisticated digital enterprise. By utilizing the tutorials and best practices found in the Azure IaaS Resource Center, organizations can ensure that their infrastructure is not just a place to run applications, but a durable platform capable of withstanding the unpredictable nature of the digital world.