Sherlock: Unlocking the Public Online Footprint of Usernames Across the Digital Landscape
In the intricate world of digital investigation and online presence mapping, the initial steps often involve a fundamental question: where does a specific username manifest across the vast expanse of the internet? While comprehensive Open Source Intelligence (OSINT) toolkits offer deep dives, a crucial preliminary phase necessitates a more focused approach. This is precisely the domain occupied by Sherlock, an open-source command-line utility designed to efficiently uncover a username’s public digital footprint across hundreds of websites and social platforms, thereby streamlining the process of initial research before more in-depth manual investigation is undertaken.
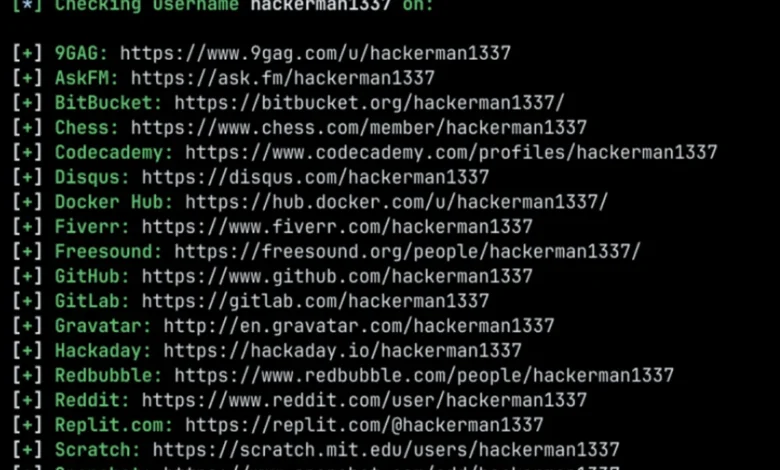
Sherlock, developed and maintained by the sherlock-project team, is a testament to the power of focused utility in the OSINT landscape. It automates the often tedious and repetitive task of manually checking individual websites for the presence of a given username. Instead of opening browser tabs one by one to test handles on platforms like GitHub, Reddit, Instagram, TikTok, or a myriad of lesser-known sites, users can simply provide a username to Sherlock, and it systematically queries a vast, pre-defined list of supported online services. This efficiency is particularly valuable for professionals and individuals who regularly need to establish the public online identity associated with a particular digital handle.
The Genesis and Functionality of Sherlock
The development of tools like Sherlock stems from a growing recognition of the pervasive nature of username reuse across the internet. Many individuals and entities adopt a consistent handle, or a close variation thereof, for their online activities. This common practice, while convenient for users, creates a trail that can be followed. Sherlock capitalizes on this phenomenon by building probable profile URLs for each supported platform, submitting queries, and analyzing the responses. The project documentation indicates support for checks across over 400 websites and social networks, offering a broad sweep of a user’s public digital presence.
Crucially, Sherlock operates within the bounds of publicly accessible information. It does not possess the capability to bypass privacy settings, access private accounts, or unearth clandestine data. Its strength lies in its ability to identify publicly visible usernames and patterns associated with public profiles. This makes it an approachable OSINT tool, requiring no API keys, browser extensions, or complex setup procedures to begin operation. Its reliance on Python as its core language also makes it relatively accessible for those familiar with the ecosystem.
What Sherlock Empowers Users To Do
The practical applications of Sherlock are diverse and impactful across various professional fields. For journalists, it can aid in verifying the online presence of sources or subjects of their investigations. OSINT researchers and security analysts leverage it to quickly map out an individual’s or organization’s public digital footprint, identifying potential connections and platforms of interest. Recruiters might use it to gain a broader understanding of a candidate’s online professional presence, while investigators can use it as a preliminary step in tracing individuals or entities. Even creators and ordinary users can benefit from understanding how their chosen usernames are represented across the web.
Sherlock’s core functionality can be summarized by its ability to:
- Identify Username Availability: Determine if a specific username is already in use on a multitude of platforms.
- Discover Public Profiles: Locate public profiles associated with a given username across a wide array of websites and social media networks.
- Map Digital Footprints: Provide an initial overview of where a username appears online, serving as a starting point for more granular research.
- Detect Username Reuse: Highlight instances where the same or similar usernames are employed across different platforms, indicating a consistent online identity.
- Streamline Initial Reconnaissance: Significantly reduce the time and effort required for the initial phase of online presence investigation.
Installation and Accessibility
The sherlock-project team has striven to make Sherlock easily accessible to its intended user base. Several installation methods are provided, catering to different user preferences and technical environments.
- Installation via pipx: For users seeking a clean, isolated installation at the user level,
pipxis recommended. The commandpipx install sherlock-projecthandles the process efficiently.pipxis a tool for installing and running Python applications in isolated environments. - Installation via pip: For those who prefer to use the standard Python package installer,
pipcan be used with the commandpip install --user sherlock-project. This installs the package for the current user. - Running with Docker: Users who wish to avoid direct Python package installations can opt for Docker. The command
docker run -it --rm sherlock/sherlockprovides a containerized environment to run Sherlock. This is particularly useful for maintaining a clean system or for users who frequently work with containerized applications. - Other Package Sources: The project also acknowledges community-maintained packages for various Linux distributions and package managers, including Debian, Ubuntu, Homebrew, Kali, and BlackArch. However, it is important to note that these are not directly maintained by the Sherlock Project, and the
pipxinstallation is generally considered the safest and most recommended default.
Navigating the Sherlock Interface and Usage
Once installed, operating Sherlock is designed to be straightforward. The fundamental command structure involves invoking the sherlock executable followed by the target username.
The basic command for searching a single username is:
sherlock user123
This command will initiate a search for the username "user123" across all supported sites and, by default, save the results to a text file named after the username in the current directory.
Sherlock offers a range of common options to refine search queries and control output:
--site <site_name>: This option allows users to specify particular websites or platforms to search within. This is incredibly useful for narrowing down the search to platforms that are most relevant to the investigation, saving time and reducing noise in the results. For instance,sherlock johndoe --site GitHub --site Redditwould limit the search to only GitHub and Reddit.--print-found: This flag instructs Sherlock to only display the results for sites where the username was found, rather than listing all attempted sites. This makes the output more concise and immediately actionable.--print-all: Conversely, this option will display results for all sites checked, whether the username was found or not. This can be useful for understanding the scope of the search and identifying platforms that were queried.--csv: This option outputs the results in a comma-separated values (CSV) format, which is ideal for importing into spreadsheets or databases for further analysis and organization.--output <filename>: This allows users to specify a custom filename for the output file, overriding the default naming convention.--json: Outputs results in JSON format, suitable for programmatic parsing.--verbose: Provides more detailed output during the execution, which can be helpful for debugging or understanding the tool’s internal processes.--nocolor: Disables colored output, which can be useful in certain scripting environments.
An Illustrative Workflow
Consider an example scenario where an investigator needs to determine the online presence of a hypothetical individual using the username "johndoe." A typical workflow might involve the following steps:
-
Initial Broad Search and Review:
sherlock johndoe --print-found
This command will execute a comprehensive search and display only the platforms where "johndoe" was found. This provides a quick overview of the username’s reach. -
Exporting Results for Detailed Analysis:
If the initial results are promising and require later review or integration into a larger report, the user can export them in a structured format:
sherlock johndoe --print-found --csv
This command will output the found profiles in CSV format, making it easy to open in spreadsheet software and meticulously examine each entry. -
Targeted Search for Key Platforms:
If the investigator already has a strong suspicion about which platforms are most relevant (e.g., professional networking sites, major social media platforms), they can narrow the search considerably:
sherlock johndoe --site GitHub --site LinkedIn --site Twitter
This approach prioritizes efficiency by focusing on pre-selected, high-probability platforms, rather than expending resources on less relevant ones. This is often the more practical approach when a few specific platforms are of greater interest than exhaustive coverage.
Strengths, Limitations, and Analytical Insights
Sherlock’s primary strengths lie in its speed and extensive coverage. It excels at automating a task that would otherwise be incredibly time-consuming and prone to human error. By integrating with a vast repository of website structures and patterns, it can rapidly scan hundreds of online properties. This makes it an invaluable tool for the initial stages of any OSINT investigation, providing a rapid assessment of a username’s public digital footprint.
However, it is crucial to acknowledge Sherlock’s inherent limitations. These are not flaws in its design but rather inherent characteristics of its function:
- Public Information Only: As previously stated, Sherlock strictly operates on publicly accessible data. It cannot penetrate private profiles or bypass any form of security or privacy settings. The information it retrieves is what anyone with a web browser and the correct URL could potentially find.
- Username Reuse is Not Definitive Proof of Identity: The most significant limitation, and one that warrants careful consideration, is that finding the same username across multiple platforms does not automatically confirm that all these accounts belong to the same individual. Variations in username usage, shared accounts, or even deliberate impersonation can lead to misleading associations. Sherlock provides leads, not definitive proof of identity. For example, if "coolhandle99" appears on five different platforms, it signifies the presence of that username but does not definitively prove a single owner across all. Further manual investigation, correlation of profile details (where public), and contextual analysis are essential to establish identity.
- Dynamic Web Structures: The internet is a constantly evolving landscape. Websites frequently update their structures, URLs, and content delivery mechanisms. While the sherlock-project team endeavors to maintain its database of supported sites and patterns, there may be instances where Sherlock’s queries are rendered ineffective due to recent website changes. Community contributions and regular updates are vital to ensuring its continued efficacy.
- Platform-Specific Nuances: Some platforms might employ subtle variations in how they handle username display or profile URLs, which could potentially elude Sherlock’s current pattern recognition.
Broader Impact and Implications in the Digital Age
The proliferation of tools like Sherlock underscores a significant trend in digital investigation and personal online security: the increasing importance of understanding one’s public digital footprint. In an era where online identities can have tangible real-world consequences, the ability to quickly assess how one is represented online is paramount.
For security researchers, Sherlock offers a rapid method to identify potential vulnerabilities or social engineering vectors related to a target’s online presence. For recruiters, it provides a preliminary glance at a candidate’s online persona, complementing formal application processes. For journalists and investigators, it serves as an indispensable first step in corroborating information or establishing initial points of contact. For ordinary users, it can be a powerful tool for self-auditing their online presence, ensuring that their digital identities align with their intentions and privacy expectations.
The existence and utility of Sherlock also highlight the ongoing tension between online privacy and the inherent discoverability of public information. While the tool respects privacy by only accessing public data, its very effectiveness in mapping public trails raises questions about the long-term implications of username consistency and the ease with which online identities can be pieced together. This dynamic fuels a continuous evolution in both the tools used for investigation and the strategies employed for digital privacy management.
Conclusion
Sherlock is a focused, efficient, and remarkably practical tool for anyone needing to quickly ascertain the public online presence associated with a given username. It excels at automating a tedious but essential task, providing a valuable starting point for deeper investigations. While its outputs should always be treated as leads rather than definitive conclusions, its ability to scan hundreds of platforms rapidly makes it an indispensable asset in the modern digital investigation toolkit. By democratizing access to preliminary online footprint analysis, Sherlock empowers a wide range of users to navigate the complex digital landscape with greater insight and efficiency. Its continued development and community support are vital to its ongoing relevance in the ever-evolving world of online information.