Navigating the New Era of Digital Sovereignty: From Privacy Compliance to Operational Resilience in an Unstable Global Landscape

In a high-level summit held in Brussels, global policymakers, IT leaders, and representatives from regulated industries gathered to redefine the parameters of digital sovereignty, signaling a move from theoretical debate toward a practical leadership discipline. Digital sovereignty is no longer viewed through the narrow lens of legal compliance or data privacy; instead, it has emerged as a critical component of national security, economic continuity, and risk management. As governments and enterprises navigate an increasingly volatile geopolitical climate, the focus has shifted toward maintaining operational control over critical infrastructure and ensuring that the adoption of transformative technologies, such as artificial intelligence, does not result in a loss of institutional or national autonomy.
The transition from "privacy-first" to "resilience-first" strategies reflects a maturing digital landscape. While the General Data Protection Regulation (GDPR) set the initial standard for data handling, the modern executive is now faced with a more complex set of questions: How can a nation ensure its public services remain functional during a regional network outage? How can a regulated bank maintain its operations if a geopolitical shift restricts access to global cloud providers? These concerns have moved from IT departments to boardrooms, driving a fundamental change in how trust is evaluated in digital systems.
A Decade of Regulatory Evolution: A Chronology of Digital Governance
The current emphasis on digital sovereignty is the culmination of over a decade of regulatory friction and technological advancement. To understand the present landscape, one must look at the timeline that brought the industry to this juncture in Brussels.
The journey began in earnest in 2016 with the adoption of the GDPR, which went into full effect in 2018. This landmark legislation established the principle that data belonging to individuals within the European Union must be protected regardless of where it is processed. This was followed by the 2020 "Schrems II" ruling by the Court of Justice of the European Union, which invalidated the EU-U.S. Privacy Shield, forcing organizations to re-evaluate the legal basis for transatlantic data transfers.
By 2022, the conversation expanded beyond privacy. The concept of "Strategic Autonomy" became a central pillar of EU policy, leading to the proposal of the Data Act and the expansion of the European Alliance for Industrial Data, Edge, and Cloud. In early 2024, the implementation of the EU AI Act further complicated the sovereignty landscape, requiring that high-risk AI systems adhere to strict standards of transparency and local oversight. The Brussels summit marks the latest chapter in this progression, where the focus has moved from creating rules to implementing technical solutions that can survive "worst-case" scenarios, such as total network disconnection or severe geopolitical decoupling.
The Shift from Privacy to Operational Resilience
While privacy remains a foundational element of digital sovereignty, it is no longer the sole metric for success. Today, customers in critical sectors—such as energy, healthcare, and finance—are increasingly preoccupied with business continuity. The threat of state-sponsored cyberattacks, supply chain disruptions, and physical damage to subsea cables has elevated "resilience" to a top-tier priority.
For many organizations, sovereignty now means understanding the "blast radius" of a potential failure. They are asking whether their critical workloads can operate if connectivity to a primary region is constrained or if a policy change by a foreign government suddenly alters the terms of service. This has led to a demand for "sovereign cloud" environments that offer not just data residency, but operational autonomy.
The innovation pressure added by generative AI has intensified this need. As AI becomes central to public service delivery and national competitiveness, organizations cannot afford to wait for the resolution of sovereignty debates before deploying new tools. The challenge lies in moving forward with AI adoption while maintaining the ability to audit, control, and, if necessary, isolate the data and models powering these systems.
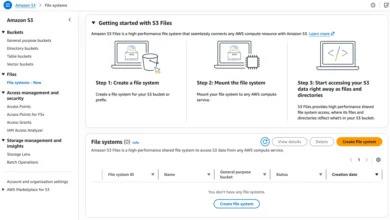
Technical Implementations: The EU Data Boundary and Disconnected Operations
In response to these evolving requirements, technology providers are moving toward a "consultative risk management" approach. This model rejects a one-size-fits-all solution in favor of a continuum of deployment options. At the most accessible end of this spectrum are public cloud services with enhanced residency and encryption controls. At the more extreme end are "air-gapped" or disconnected environments.
A significant milestone in this technical evolution is the EU Data Boundary. This initiative allows customers to store and process their data exclusively within the EU and European Free Trade Association (EFTA) regions. By providing a clear geographical limit for data lifecycle management, it addresses the primary concerns of European regulators. However, the Brussels summit highlighted that data residency is only part of the solution.

Recent developments have seen the expansion of "disconnected operations" for sovereign clouds. These solutions allow critical workloads—including large-scale AI models—to run in environments that are completely severed from the public internet. This capability is vital for defense agencies, emergency services, and critical infrastructure operators who must maintain functionality even during a total communications blackout. By retaining consistent governance and operational control across both connected and disconnected settings, organizations can bridge the gap between innovation and security.
Supporting Data: The Economics and Risks of Sovereignty
The push for digital sovereignty is backed by significant economic and security data. According to industry reports from IDC, spending on sovereign cloud solutions is expected to grow significantly faster than the general cloud market over the next five years. Governments in Europe and Asia are increasingly earmarking portions of their IT budgets specifically for "sovereign-compliant" infrastructure.
Furthermore, the rise in state-sponsored cyber activity has underscored the risk of over-dependence on centralized, non-sovereign systems. In 2023, cyber-resilience became a primary driver for cloud migration, with 70% of surveyed IT leaders in regulated industries citing "national security concerns" as a factor in their architectural decisions. The cost of data breaches in highly regulated sectors also continues to climb, with the average cost of a healthcare data breach exceeding $10 million, further incentivizing the adoption of sovereign controls that limit external exposure.
Industry and Policy Reactions
The consensus in Brussels was that digital sovereignty should not be a "checkbox" exercise but a dynamic posture. Policy experts at the summit noted that the era of "abstract assurances" is over. Regulators are now demanding transparency into how cloud systems are governed and how exceptional situations—such as law enforcement requests from foreign jurisdictions—are managed.
Representatives from European institutions emphasized that "Strategic Autonomy" does not mean protectionism or isolationism. Instead, it is about ensuring that European organizations have a choice. "Sovereignty is about the freedom to choose your dependencies and the power to manage them," noted one policy advisor during a panel discussion. This sentiment was echoed by IT leaders who expressed that they do not want to sacrifice the scale and innovation of global cloud providers, but they do require the "kill switches" and localized controls that allow them to fulfill their domestic obligations.
The AI Frontier and Sovereign Intelligence
Perhaps the most significant new frontier in this debate is "Sovereign AI." As nations recognize that AI will be the engine of future economic growth, there is a growing movement to develop national AI capabilities. This involves not only the hardware (GPUs) but also the data used to train models and the infrastructure used to run them.
The Brussels summit addressed the risk of "intelligence dependency," where a nation relies entirely on foreign-owned and operated AI models for its most sensitive functions. To mitigate this, Microsoft and other providers are beginning to offer support for running large-scale AI models within sovereign boundaries. This allows governments to leverage the power of frontier models while ensuring that the underlying data—and the resulting insights—remain under local jurisdiction.
Implications for the Future: From Rhetoric to Implementation
As digital sovereignty becomes embedded in procurement and policy, the future will be defined by implementation rather than rhetoric. The Brussels meeting served as a reminder that trust is built over time through consistent action and transparency. For leaders, the path forward involves three key actions:
First, organizations must perform a workload-by-workload risk assessment. Not every piece of data requires an air-gapped environment, but critical national infrastructure certainly does. Second, there must be a move toward "sovereignty by design," where architectural reviews prioritize resilience and local control from the outset. Finally, there must be ongoing collaboration between the public and private sectors to ensure that regulations remain practical and that technology continues to evolve in alignment with democratic values.
Ultimately, digital sovereignty is not a destination but a continuous discipline. In an age of global uncertainty, the ability to operate with confidence—regardless of geopolitical shifts or technological disruptions—is the most valuable asset any organization or nation can possess. The discussions in Brussels confirm that while the challenges are significant, the tools to address them are becoming increasingly sophisticated, allowing for a future where innovation and control can coexist.