Microsoft has simplified service mesh scaling and management with an ambient-based service network for AKS. Here’s how to get started.

The landscape of cloud-native orchestration has reached a significant turning point with Microsoft’s introduction of the Azure Kubernetes Application Network. This new service, currently in preview, marks a shift away from the resource-intensive "sidecar" architecture that has defined service mesh implementations for nearly a decade. By leveraging the "ambient" mode of the Istio service mesh, Microsoft is offering Azure Kubernetes Service (AKS) users a managed, transparent networking layer that promises to reduce operational complexity and hardware overhead while maintaining high standards for security and observability.
As organizations increasingly migrate critical workloads to Kubernetes, the challenge of managing microservices at scale has become a primary bottleneck. Traditionally, a service mesh required injecting a proxy container—known as a sidecar—into every single application pod. While effective for securing traffic and gathering telemetry, this "sidecar tax" often resulted in significant increases in memory and CPU consumption, alongside a heightened management burden for platform engineering teams. The Azure Kubernetes Application Network seeks to eliminate these frictions by moving the service mesh functionality into the infrastructure layer itself.
The Evolution of Service Mesh Architecture
To understand the significance of Microsoft’s latest offering, it is necessary to examine the historical trajectory of service mesh technology. In the early days of Kubernetes, networking between services was largely unmanaged, leading to security vulnerabilities and a lack of visibility into inter-service communication. The emergence of projects like Istio and Linkerd solved these issues by introducing the sidecar model. In this model, every application container is paired with a network proxy (usually Envoy) that intercepts all incoming and outgoing traffic.
While the sidecar model provided a robust control plane, it introduced three primary challenges. First, it required application pods to be restarted whenever the proxy needed an update. Second, it consumed substantial resources, as even small applications were forced to run a secondary proxy container. Third, the complexity of configuring and troubleshooting thousands of individual proxies necessitated a specialized discipline known as platform engineering.
The shift toward "ambient" mesh represents the next phase of this evolution. Announced by the Istio project in late 2022, ambient mode separates the service mesh into two distinct layers: a zero-trust tunnel (ztunnel) for secure transport and an optional Layer 7 (L7) processing layer for complex traffic routing and policy enforcement. By removing the proxy from the application pod and placing it at the node level, Microsoft can now offer a "sidecar-less" experience that is both more efficient and easier to manage.
Understanding the Azure Kubernetes Application Network
The Azure Kubernetes Application Network is described by Microsoft as a fully managed, ambient-based service network solution. It is designed specifically for AKS, integrating deeply with existing Azure services like Microsoft Entra (formerly Azure AD) and Azure Key Vault. This integration ensures that identity management and certificate rotation—two of the most difficult aspects of service mesh management—are handled automatically by the Azure control plane.
The architecture of this new service is split into two functional tiers. The core tier consists of node-level application proxies that manage basic connectivity and security. This ensures that all traffic between nodes is encrypted via Mutual TLS (mTLS) by default, without requiring any configuration changes to the application code. The second tier involves lower-level proxies that support advanced routing, network policies, and sophisticated traffic management.
One of the most compelling features of this managed service is its ability to facilitate migrations from deprecated technologies. For example, many AKS users currently rely on the ingress-nginx controller, which is increasingly being supplanted by the Kubernetes Gateway API. The Azure Kubernetes Application Network provides a bridge for these users, allowing them to adopt the Gateway API and ambient mesh features while maintaining their existing ingress configurations during the transition period.
Chronology of Development and Microsoft’s Open Source Commitment
The path to the Azure Kubernetes Application Network began several years ago when Microsoft first integrated Istio into the AKS ecosystem. Historically, Microsoft supported the Service Mesh Interface (SMI) and various other networking standards, but the industry eventually consolidated around Istio as the dominant service mesh provider.
In early 2024, Microsoft intensified its contributions to the Istio project, specifically focusing on the stability of ambient mode. By KubeCon + CloudNativeCon Europe 2026, Microsoft officially announced that ambient mesh would serve as the backbone for its next-generation application networking on Azure. This move aligns with Microsoft’s broader strategy of adopting open-source standards and providing them as "opinionated" managed services, reducing the "DIY" burden on enterprise customers.
The timeline for the current rollout started with a private preview for select enterprise partners, followed by the current public preview available in major Azure regions including East US, West Europe, and Southeast Asia. Microsoft has indicated that general availability will follow once the service meets specific performance benchmarks and broadens its support for various node pool types.
Technical Implementation and Data Plane Mechanics
The technical heart of the Azure Kubernetes Application Network is the ztunnel. Unlike a sidecar proxy, a ztunnel runs as a daemon on each Kubernetes node. When a service in Pod A wants to communicate with a service in Pod B, the request is intercepted by the local ztunnel. The proxy then establishes a Secure Overlay (HBONE – HTTP-Based Overlay Network) to the ztunnel on the destination node.
This approach offers several technical advantages:
- Reduced Resource Overhead: Because there is only one
ztunnelper node rather than one proxy per pod, the total memory footprint of the service mesh is reduced by an estimated 70% to 90% in large-scale deployments. - Simplified Lifecycle Management: Node-level proxies can be patched and updated by Microsoft without restarting application containers, ensuring zero downtime for the business logic.
- Improved Performance: By reducing the number of "hops" a packet takes through various proxy layers, ambient mode can lower latency for simple L4 (Layer 4) traffic.
For more complex requirements, such as path-based routing or rate limiting, the system utilizes "Waypoint proxies." These are separate pods that handle Layer 7 logic for a specific namespace or service. This decoupled architecture allows users to pay the "performance cost" of L7 processing only where it is strictly necessary, rather than applying it globally.
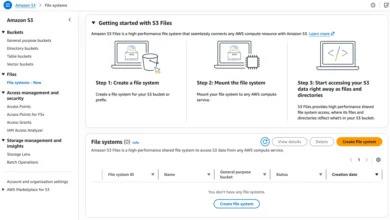
Getting Started: A Step-by-Step Guide
To begin using the Azure Kubernetes Application Network, developers must first ensure their environment meets the prerequisite requirements. The service requires the Azure CLI and an active AKS cluster with Microsoft Entra integration and OpenID Connect (OIDC) enabled.
The process begins with the registration of the AppNet provider:
- Register the Service: Users must register the
Microsoft.ServiceNetworkprovider in their Azure subscription. - Install Extensions: The
appnetextension for the Azure CLI must be installed to manage the mesh. - Create the Application Network: Using the command
az appnet create, users define a logical network that will house the mesh configurations. - Join Clusters: Existing or new AKS clusters are then "joined" to the Application Network. During this phase, users can choose between "Automatic" or "Manual" upgrade modes, with the former allowing Microsoft to handle all security patches and version increments.
- Enable Ambient Mode: Finally, specific namespaces within the cluster are labeled to opt-in to the ambient mesh. Once labeled, the
ztunnelsautomatically begin intercepting traffic for pods in those namespaces.
Analysis of Implications for DevOps and Platform Engineering
The introduction of a managed ambient service mesh represents a significant shift in the division of labor within IT organizations. Traditionally, the service mesh was the domain of the platform engineer—a specialist tasked with the unenviable job of managing YAML configurations and troubleshooting proxy sidecars.
By abstracting these complexities into a managed Azure service, Microsoft is effectively "democratizing" service mesh capabilities. Application developers can now implement secure, encrypted communication and advanced traffic routing without needing deep expertise in Istio’s internal architecture. This shift allows platform engineers to move away from mundane maintenance tasks and focus on higher-value activities like architectural governance and cost optimization.
Furthermore, the "ambient" nature of the service provides a more predictable cost model. Because the resource consumption is tied to the number of nodes rather than the number of pods, organizations can scale their applications (horizontal pod autoscaling) without a linear increase in the "mesh tax." This makes AKS a more competitive platform for high-density microservices environments.
Current Limitations and Future Outlook
While the Azure Kubernetes Application Network offers a glimpse into the future of cloud networking, the current preview phase includes several notable restrictions. It does not yet support Windows Server node pools, nor is it available for "private" AKS clusters that lack public internet egress. Additionally, because the service is built on Istio, it cannot coexist with other Istio installations on the same cluster, requiring a "clean" migration for existing Istio users.
Microsoft has signaled that future updates will focus on multi-region connectivity, allowing the Application Network to bridge clusters across different geographical zones seamlessly. There is also a planned integration with Azure Firewall and Azure Web Application Firewall (WAF) to provide a unified security posture from the edge of the internet down to the individual microservice.
As the industry moves closer to a "serverless" mentality for infrastructure, the Azure Kubernetes Application Network stands as a major milestone. It fulfills the promise of Kubernetes by providing a truly transparent infrastructure layer where networking, security, and observability are provided as a utility, rather than a burden. For organizations looking to modernize their stack, the transition from sidecars to ambient mesh on AKS represents a clear path toward greater efficiency and reduced operational risk.