Russian Intelligence Exploits Thousands of Legacy Routers to Siphon Microsoft User Data in Global Espionage Campaign
Cybersecurity researchers and government agencies have issued a high-level alert regarding a sophisticated yet structurally simple espionage campaign orchestrated by Russian military intelligence. The operation, attributed to the state-sponsored threat actor known as Forest Blizzard, has successfully compromised more than 18,000 internet routers globally to harvest authentication tokens from Microsoft Office users. Unlike traditional cyberattacks that rely on the deployment of complex malicious software, this campaign utilizes "old-school" techniques to bypass modern security measures, including multi-factor authentication (MFA). By targeting vulnerabilities in older, end-of-life hardware, the attackers have managed to maintain a stealthy presence across thousands of networks, siphoning sensitive data from government agencies, law enforcement, and private consumers alike.
The scale of the operation was revealed in a series of coordinated reports from Microsoft’s Threat Intelligence team, the UK’s National Cyber Security Centre (NCSC), and Black Lotus Labs, the security arm of internet backbone provider Lumen. According to these findings, the campaign reached its zenith in late 2025 and continued into early 2026, marking a significant shift in how Russian intelligence units approach large-scale data theft. By focusing on the infrastructure of the Small Office/Home Office (SOHO) market, Forest Blizzard has exploited the weakest links in the global digital chain to gain access to high-value targets.
The Mechanics of DNS Hijacking and Token Theft
At the heart of this campaign is a technique known as Domain Name System (DNS) hijacking. DNS serves as the internet’s phonebook, translating human-readable web addresses, such as "outlook.office.com," into the numerical IP addresses that computers use to communicate. By exploiting known vulnerabilities in legacy routers—specifically older models from manufacturers like Mikrotik and TP-Link—Forest Blizzard gained administrative access to these devices. Once inside, the hackers did not install malware; instead, they simply reconfigured the routers’ DNS settings.
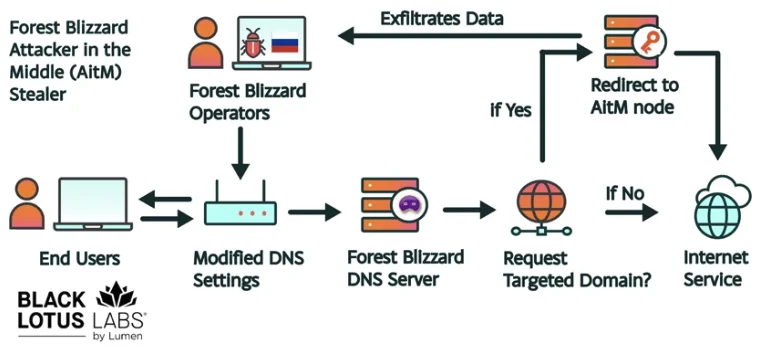
By pointing the routers to attacker-controlled DNS servers, the group could intercept and redirect traffic at will. When a user on a compromised network attempted to access Microsoft services, the rogue DNS server directed their connection through a "middleman" server controlled by the GRU. This allowed the attackers to perform an Adversary-in-the-Middle (AiTM) attack on Transport Layer Security (TLS) connections.
The primary objective of this redirection was the harvesting of OAuth authentication tokens. In modern cloud environments, these tokens are generated after a user successfully logs in and completes any required multi-factor authentication. The token acts as a digital "key" that allows the user to remain logged in without re-entering credentials. By capturing these tokens as they were transmitted across the hijacked network, Forest Blizzard could impersonate users and gain full access to their Outlook emails and other Office 365 data. Because the token is generated after the MFA process, the attackers effectively bypassed the very security protocols designed to stop them.
Profiling the Threat Actor: Forest Blizzard (APT28)
Forest Blizzard, also known by the aliases APT28, Fancy Bear, and Strontium, is a notorious cyber-espionage group linked to Unit 26165 of Russia’s General Staff Main Intelligence Directorate (GRU). The group has a long history of high-stakes political interference and industrial espionage. Most notably, APT28 was identified as the entity responsible for the 2016 breaches of the Democratic National Committee (DNC) and the Hillary Clinton presidential campaign, operations intended to influence the outcome of the U.S. election.
The group’s shift toward DNS hijacking at scale represents a tactical evolution. Historically, APT28 relied on spear-phishing and custom malware payloads. However, as defensive technologies like Endpoint Detection and Response (EDR) have become more adept at spotting malicious files, the group has moved toward "living off the land" techniques. By manipulating the fundamental protocols of the internet—like DNS—they can achieve their goals without leaving a traditional digital footprint on the victim’s computer.
Black Lotus Labs noted that this move toward a "malware-less" approach followed a period of tactical experimentation. In mid-2025, the group was observed using malware to control a small, highly targeted group of routers. Following a public exposure of those tactics by the NCSC in August 2025, Forest Blizzard immediately pivoted. Within 24 hours of the report’s release, the group abandoned its malware-based strategy in favor of the systemic, mass-scale DNS hijacking observed in the current campaign.
Chronology of the Espionage Campaign
The timeline of the Forest Blizzard operation illustrates a rapid escalation in activity and a keen ability to adapt to public disclosures by security firms.
- August 2025: The UK’s National Cyber Security Centre (NCSC) releases a report detailing APT28’s use of malware to compromise edge devices. In response, the group almost immediately shifts its infrastructure to a DNS-based hijacking model to avoid detection.
- September – November 2025: The group begins scanning for and compromising vulnerable SOHO routers globally, focusing on devices that are end-of-life or lack recent security patches.
- December 2025: The campaign reaches its peak. Black Lotus Labs identifies over 18,000 compromised routers within the surveillance dragnet. Targeted entities include foreign ministries, law enforcement agencies in Europe and North America, and third-party email providers.
- January – March 2026: Microsoft and Lumen track the redirection of traffic from over 200 high-value organizations. The attackers successfully harvest thousands of OAuth tokens, providing them with persistent access to sensitive government and corporate communications.
- March 23, 2026: In a broader response to the threat of foreign-made networking equipment, the U.S. Federal Communications Commission (FCC) announces a sweeping policy change, refusing to certify new consumer-grade routers produced outside the United States.
- April 7, 2026: Microsoft and its security partners go public with the details of the Forest Blizzard campaign, issuing urgent remediation guidance for affected users and network administrators.
Supporting Data and Impacted Infrastructure
The sheer volume of the data collected by researchers underscores the gravity of the breach. Microsoft identified more than 5,000 consumer devices and 200 distinct organizations caught in the net. The geographic distribution of the compromised routers was global, though there was a clear concentration in regions of strategic interest to the Russian state.

The hardware targeted was predominantly "legacy" equipment. Mikrotik and TP-Link routers, common in small offices and home environments, were the primary targets. Many of these devices were no longer receiving firmware updates from their manufacturers, making them "perpetually vulnerable" to known exploits. Because many employees now work from home (WFH), a compromise of a residential router can provide a gateway into a corporate or government network, as the user’s professional traffic passes through the hijacked home hardware.
Ryan English, a security engineer at Black Lotus Labs, emphasized the simplicity of the attack. "These guys didn’t use sexy, high-tech malware," English stated. "They used a graybeard approach—altering DNS—that worked because so many people ignore the security of their routers. It’s an old-school method that is devastatingly effective in a modern, cloud-reliant world."
Regulatory Response and the FCC "Covered List"
The revelation of the Forest Blizzard campaign has accelerated a significant shift in U.S. telecommunications policy. On March 23, 2026, the Federal Communications Commission (FCC) updated its "Covered List" to include a broad ban on the certification of consumer-grade internet routers manufactured in foreign "adversarial" nations.
The FCC warned that the security of these devices has become a matter of national survival. "Foreign-made routers have become an untenable national security threat," the commission stated in its announcement. "Poorly secured routers present a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons."
This policy change has met with mixed reactions from industry experts. While security advocates applaud the move to harden the supply chain, others point out the logistical challenges. Currently, the vast majority of consumer networking equipment is manufactured in East Asia. Under the new rules, few routers would be eligible for sale in the U.S. without special "conditional approval" from the Department of Homeland Security or the Department of War. Critics argue this could lead to a domestic shortage of hardware or significant price increases, though proponents suggest it will catalyze a return to domestic high-tech manufacturing.
Implications for Global Cybersecurity
The Forest Blizzard campaign highlights a critical blind spot in modern cybersecurity: the "edge" device. While corporations have spent billions securing servers and endpoints (laptops and phones), the routers that connect these devices to the internet are often neglected.
The use of DNS hijacking to steal OAuth tokens also signals a need for a more robust approach to identity management. If a successful login and MFA challenge can be bypassed by stealing a token at the network level, then the industry must look toward "Continuous Access Evaluation" (CAE). This technology allows service providers like Microsoft to revoke tokens instantly if a change in the user’s network location or security posture is detected.
Furthermore, the "Work from Home" era has blurred the lines between consumer and enterprise security. A state-sponsored actor no longer needs to breach a highly fortified government data center if they can simply compromise the $50 router in a diplomat’s home office.
Remediation and Future Outlook
For organizations and individuals, the primary defense against such attacks is the immediate replacement of end-of-life hardware. Security experts recommend that any router no longer receiving active firmware updates be decommissioned. Additionally, network administrators are urged to monitor for unauthorized changes to DNS settings and to implement encrypted DNS protocols, such as DNS over HTTPS (DoH) or DNS over TLS (DoT), which can prevent the kind of hijacking used by Forest Blizzard.
As the geopolitical landscape remains tense, the GRU and other state-backed actors are expected to continue refining these low-noise, high-impact techniques. The battle for the internet’s infrastructure is no longer just about stopping viruses; it is about ensuring the integrity of the very protocols that hold the web together. The Forest Blizzard campaign serves as a stark reminder that in the world of global espionage, the simplest methods are often the most dangerous.








