Sanctioned Cryptocurrency Exchange Grinex Halts Operations Following 13.7 Million Dollar Cyberattack and Allegations of State-Sponsored Sabotage

Grinex, a Kyrgyzstan-incorporated cryptocurrency exchange that has faced intense scrutiny and sanctions from both United States and United Kingdom authorities, has officially announced the indefinite suspension of its operations. The platform cited a catastrophic security breach occurring on April 15, 2026, which resulted in the theft of approximately $13.74 million in user assets. In a move that has sparked significant debate within the cybersecurity and geopolitical communities, the exchange has explicitly blamed Western intelligence agencies for the intrusion, characterizing the event as a coordinated effort to destabilize the financial infrastructure of the Russian Federation.
The incident, which resulted in the loss of over 1 billion rubles, represents a major escalation in the ongoing shadow war between Western financial regulators and the decentralized networks used by sanctioned entities to bypass international restrictions. According to a statement released on the Grinex website, the company’s internal digital forensic investigation suggests the attack was carried out with a level of "technological sophistication" and resource allocation typically reserved for state-level actors. The exchange argued that the breach was not a standard criminal enterprise but a strategic strike aimed at "inflicting direct damage upon Russia’s financial sovereignty."
The Anatomy of the April 15 Security Breach
The breach occurred at approximately 12:00 UTC on April 15, 2026. Blockchain analytics firms, including Elliptic and TRM Labs, began tracking the movement of illicit funds almost immediately as assets were drained from Grinex-controlled wallets. The stolen funds, primarily denominated in the stablecoin Tether (USDT), were rapidly moved across the TRON and Ethereum blockchains.
In a technical breakdown of the event, analysts noted a "frantic swapping" pattern. Once the USDT was secured in the attacker’s wallets, it was immediately converted into non-freezable assets such as Tron (TRX) or Ethereum (ETH). This tactic is a hallmark of sophisticated money laundering in the crypto space; because Tether Limited, the issuer of USDT, has the technical capability to "freeze" specific addresses at the request of law enforcement or in response to sanctions, attackers must exit the stablecoin as quickly as possible to ensure the longevity of their haul.
The speed and precision of these movements suggest a pre-planned exit strategy. While Grinex maintains this was the work of "hostile state agencies," the broader cybersecurity community remains divided. Some experts point out that the techniques used—rapid cross-chain swapping and the use of obfuscation tools—are also common among high-tier cybercriminal syndicates, such as the North Korean-linked Lazarus Group or internal "insider" threats.
The Evolution of Grinex: From Garantex to a Kyrgyz Hub
To understand the significance of the Grinex collapse, one must look at its lineage. Investigations by the U.S. Treasury’s Office of Foreign Assets Control (OFAC) and the U.K. Office of Financial Sanctions Implementation (OFSI) have consistently linked Grinex to Garantex, a notorious Russian cryptocurrency exchange.

Garantex was first sanctioned by the U.S. Treasury in April 2022. At the time, officials alleged that the exchange was a primary conduit for laundering funds derived from ransomware attacks and illicit darknet markets, including the now-defunct Hydra Market and the Conti ransomware group. Despite these sanctions, Garantex proved resilient, reportedly processing over $100 million in illicit transactions even after being blacklisted.
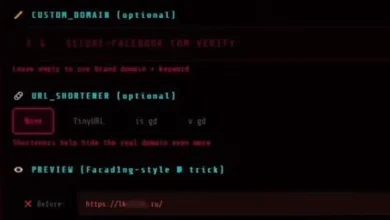
As Western pressure mounted, Garantex underwent a series of structural shifts to evade detection. This included moving its operational base to Kyrgyzstan and rebranding aspects of its service under the Grinex name. By operating out of Central Asia, the entity sought to leverage more lenient regulatory environments while maintaining a heavy presence in the Moscow financial district.
Central to this evasion strategy was the use of a ruble-backed stablecoin known as A7A5. This asset allowed users to move value in and out of the Russian financial system without interacting with the U.S. dollar-pegged stablecoins that are more easily monitored by Western authorities. The integration of A7A5 into the Grinex ecosystem made it a vital node for Russian entities seeking to maintain international liquidity amidst tightening sanctions.
The TokenSpot Connection and Regional Ripple Effects
The impact of the April 15 hack was not limited to Grinex alone. TRM Labs identified approximately 70 digital addresses connected to the incident, many of which were linked to TokenSpot, another Kyrgyzstan-based exchange. Analysts believe TokenSpot functioned as a front or a secondary liquidity provider for Grinex.
On the day of the hack, TokenSpot abruptly informed its users via Telegram that the platform would be "temporarily unavailable due to technical maintenance." While TokenSpot claimed to have resumed full operations by April 16, the breach resulted in the theft of funds from its wallets as well, albeit on a smaller scale than Grinex. The fact that the stolen funds from both Grinex and TokenSpot were routed to the same consolidation addresses confirms the deep operational ties between the two entities.
Furthermore, the role of Rapira, a Georgia-incorporated exchange with a Moscow office, has come under scrutiny. Earlier in 2026, Elliptic disclosed that Rapira had engaged in cryptoasset transactions with Grinex totaling more than $72 million. This interconnected web of exchanges across Kyrgyzstan, Georgia, and Russia highlights the sophisticated infrastructure built to facilitate the flow of capital in the face of global isolation.
Geopolitical Rhetoric vs. On-Chain Reality
The official response from Grinex has been characterized by a blend of corporate grievance and nationalist rhetoric. A company spokesperson stated that the exchange’s infrastructure had been under constant siege since its inception, claiming that Western intelligence agencies have long targeted the platform to "destabilize the domestic financial sector."

However, blockchain intelligence firms like Chainalysis have raised the possibility of a "false flag" operation. In their analysis, they noted that the "sanctioned status, restricted ecosystem, and use of Garantex’s preferred obfuscation techniques" make it worth considering whether the "hack" was an orchestrated internal event.
In the world of high-stakes cryptocurrency, "exit scams" are often disguised as hacks. By claiming a state-sponsored attack, the operators of a sanctioned exchange can effectively "zero out" their liabilities to depositors while retaining the stolen funds in private, untraceable wallets. Whether the $13.74 million was taken by a foreign intelligence service or by the exchange operators themselves, the end result remains the same: a total loss for the users and a significant disruption to a key sanctions-evasion pipeline.
Broader Implications for Global Crypto Regulation
The suspension of Grinex operations serves as a landmark event in the regulation of digital assets. It underscores the effectiveness—and the limitations—of international sanctions. While the U.S. and U.K. were able to push Grinex into the fringes of the global economy, the exchange continued to function for years by shifting jurisdictions and using regional proxies.
The collapse of Grinex is likely to lead to several outcomes in the near future:
- Increased Pressure on Central Asian Regulators: Kyrgyzstan and Georgia will likely face renewed diplomatic pressure from the FATF (Financial Action Task Force) and Western governments to tighten their oversight of cryptocurrency exchanges that cater to sanctioned Russian interests.
- The Rise of Localized Stablecoins: The use of the A7A5 stablecoin demonstrates a shift away from the "Euro-Dollar" dominance in crypto. Sanctioned states are increasingly looking to develop their own sovereign or semi-sovereign digital assets to bypass the reach of the U.S. Treasury.
- Sophistication of "False Flag" Narratives: As more sanctioned entities face liquidity crises, the "state-sponsored hack" may become a standard excuse for insolvency, requiring blockchain forensic firms to develop even more granular methods of distinguishing between external breaches and internal misappropriation.
As of late April 2026, the funds stolen from Grinex remain in several consolidated wallets, closely monitored by law enforcement and private intelligence firms. With the exchange’s website now serving as little more than a placeholder for its accusations against the West, the era of Grinex appears to have reached a definitive, if controversial, end. For the broader financial world, the incident remains a stark reminder of the volatility and geopolitical complexity inherent in the modern digital asset landscape.